1、新建挂载目录,创建数据库文件:
mkdir -p /xxx/headscale/config touch /xxx/headscale/config/db.sqlite 2、配置文件
/xxx/headscale/config/config.yaml 端口我改了,根据自己情况来
--- # headscale will look for a configuration file named `config.yaml` (or `config.json`) in the following order: # # - `/etc/headscale` # - `~/.headscale` # - current working directory # The url clients will connect to. # Typically this will be a domain like: # # https://myheadscale.example.com:443 # server_url: http://<public_ip>:8081 # Address to listen to / bind to on the server # # For production: # listen_addr: 0.0.0.0:8080 listen_addr: 0.0.0.0:8081 # Address to listen to /metrics, you may want # to keep this endpoint private to your internal # network # metrics_listen_addr: 0.0.0.0:6030 # Address to listen for gRPC. # gRPC is used for controlling a headscale server # remotely with the CLI # Note: Remote access _only_ works if you have # valid certificates. # # For production: # grpc_listen_addr: 0.0.0.0:50443 grpc_listen_addr: 127.0.0.1:50443 # Allow the gRPC admin interface to run in INSECURE # mode. This is not recommended as the traffic will # be unencrypted. Only enable if you know what you # are doing. grpc_allow_insecure: false # Private key used to encrypt the traffic between headscale # and Tailscale clients. # The private key file will be autogenerated if it's missing. # private_key_path: /etc/headscale/private.key # The Noise section includes specific configuration for the # TS2021 Noise protocol noise: # The Noise private key is used to encrypt the # traffic between headscale and Tailscale clients when # using the new Noise-based protocol. It must be different # from the legacy private key. private_key_path: /etc/headscale/noise_private.key # List of IP prefixes to allocate tailaddresses from. # Each prefix consists of either an IPv4 or IPv6 address, # and the associated prefix length, delimited by a slash. # While this looks like it can take arbitrary values, it # needs to be within IP ranges supported by the Tailscale # client. # IPv6: https://github.com/tailscale/tailscale/blob/22ebb25e833264f58d7c3f534a8b166894a89536/net/tsaddr/tsaddr.go#LL81C52-L81C71 # IPv4: https://github.com/tailscale/tailscale/blob/22ebb25e833264f58d7c3f534a8b166894a89536/net/tsaddr/tsaddr.go#L33 ip_prefixes: - fd7a:115c:a1e0::/48 - 100.64.0.0/10 # DERP is a relay system that Tailscale uses when a direct # connection cannot be established. # https://tailscale.com/blog/how-tailscale-works/#encrypted-tcp-relays-derp # # headscale needs a list of DERP servers that can be presented # to the clients. derp: server: # If enabled, runs the embedded DERP server and merges it into the rest of the DERP config # The Headscale server_url defined above MUST be using https, DERP requires TLS to be in place enabled: false # Region ID to use for the embedded DERP server. # The local DERP prevails if the region ID collides with other region ID coming from # the regular DERP config. region_id: 999 # Region code and name are displayed in the Tailscale UI to identify a DERP region region_code: "headscale" region_name: "Headscale Embedded DERP" # Listens over UDP at the configured address for STUN connections - to help with NAT traversal. # When the embedded DERP server is enabled stun_listen_addr MUST be defined. # # For more details on how this works, check this great article: https://tailscale.com/blog/how-tailscale-works/ stun_listen_addr: "0.0.0.0:3478" # List of externally available DERP maps encoded in JSON urls: - https://controlplane.tailscale.com/derpmap/default # Locally available DERP map files encoded in YAML # # This option is mostly interesting for people hosting # their own DERP servers: # https://tailscale.com/kb/1118/custom-derp-servers/ # # paths: # - /etc/headscale/derp-example.yaml paths: [] # If enabled, a worker will be set up to periodically # refresh the given sources and update the derpmap # will be set up. auto_update_enabled: true # How often should we check for DERP updates? update_frequency: 24h # Disables the automatic check for headscale updates on startup disable_check_updates: true # Time before an inactive ephemeral node is deleted? ephemeral_node_inactivity_timeout: 30m # Period to check for node updates within the tailnet. A value too low will severely affect # CPU consumption of Headscale. A value too high (over 60s) will cause problems # for the nodes, as they won't get updates or keep alive messages frequently enough. # In case of doubts, do not touch the default 10s. node_update_check_interval: 10s # SQLite config db_type: sqlite3 # For production: db_path: /etc/headscale/db.sqlite # # Postgres config # If using a Unix socket to connect to Postgres, set the socket path in the 'host' field and leave 'port' blank. # db_type: postgres # db_host: localhost # db_port: 5432 # db_name: headscale # db_user: foo # db_pass: bar # If other 'sslmode' is required instead of 'require(true)' and 'disabled(false)', set the 'sslmode' you need # in the 'db_ssl' field. Refers to https://www.postgresql.org/docs/current/libpq-ssl.html Table 34.1. # db_ssl: false ### TLS configuration # ## Let's encrypt / ACME # # headscale supports automatically requesting and setting up # TLS for a domain with Let's Encrypt. # # URL to ACME directory acme_url: https://acme-v02.api.letsencrypt.org/directory # Email to register with ACME provider acme_email: "" # Domain name to request a TLS certificate for: tls_letsencrypt_hostname: "" # Path to store certificates and metadata needed by # letsencrypt # For production: tls_letsencrypt_cache_dir: /var/lib/headscale/cache # Type of ACME challenge to use, currently supported types: # HTTP-01 or TLS-ALPN-01 # See [docs/tls.md](docs/tls.md) for more information tls_letsencrypt_challenge_type: HTTP-01 # When HTTP-01 challenge is chosen, letsencrypt must set up a # verification endpoint, and it will be listening on: # :http = port 80 tls_letsencrypt_listen: ":http" ## Use already defined certificates: tls_cert_path: "" tls_key_path: "" log: # Output formatting for logs: text or json format: text level: info # Path to a file containg ACL policies. # ACLs can be defined as YAML or HUJSON. # https://tailscale.com/kb/1018/acls/ acl_policy_path: "" ## DNS # # headscale supports Tailscale's DNS configuration and MagicDNS. # Please have a look to their KB to better understand the concepts: # # - https://tailscale.com/kb/1054/dns/ # - https://tailscale.com/kb/1081/magicdns/ # - https://tailscale.com/blog/2021-09-private-dns-with-magicdns/ # dns_config: # Whether to prefer using Headscale provided DNS or use local. override_local_dns: false # List of DNS servers to expose to clients. nameservers: - 1.1.1.1 # NextDNS (see https://tailscale.com/kb/1218/nextdns/). # "abc123" is example NextDNS ID, replace with yours. # # With metadata sharing: # nameservers: # - https://dns.nextdns.io/abc123 # # Without metadata sharing: # nameservers: # - 2a07:a8c0::ab:c123 # - 2a07:a8c1::ab:c123 # Split DNS (see https://tailscale.com/kb/1054/dns/), # list of search domains and the DNS to query for each one. # # restricted_nameservers: # foo.bar.com: # - 1.1.1.1 # darp.headscale.net: # - 1.1.1.1 # - 8.8.8.8 # Search domains to inject. domains: [] # Extra DNS records # so far only A-records are supported (on the tailscale side) # See https://github.com/juanfont/headscale/blob/main/docs/dns-records.md#Limitations # extra_records: # - name: "grafana.myvpn.example.com" # type: "A" # value: "100.64.0.3" # # # you can also put it in one line # - { name: "prometheus.myvpn.example.com", type: "A", value: "100.64.0.3" } # Whether to use [MagicDNS](https://tailscale.com/kb/1081/magicdns/). # Only works if there is at least a nameserver defined. magic_dns: true # Defines the base domain to create the hostnames for MagicDNS. # `base_domain` must be a FQDNs, without the trailing dot. # The FQDN of the hosts will be # `hostname.user.base_domain` (e.g., _myhost.myuser.example.com_). base_domain: example.com # Unix socket used for the CLI to connect without authentication # Note: for production you will want to set this to something like: unix_socket: /etc/headscale/headscale.sock unix_socket_permission: "0770" # # headscale supports experimental OpenID connect support, # it is still being tested and might have some bugs, please # help us test it. # OpenID Connect # oidc: # only_start_if_oidc_is_available: true # issuer: "https://your-oidc.issuer.com/path" # client_id: "your-oidc-client-id" # client_secret: "your-oidc-client-secret" # # Alternatively, set `client_secret_path` to read the secret from the file. # # It resolves environment variables, making integration to systemd's # # `LoadCredential` straightforward: # client_secret_path: "${CREDENTIALS_DIRECTORY}/oidc_client_secret" # # client_secret and client_secret_path are mutually exclusive. # # # The amount of time from a node is authenticated with OpenID until it # # expires and needs to reauthenticate. # # Setting the value to "0" will mean no expiry. # expiry: 180d # # # Use the expiry from the token received from OpenID when the user logged # # in, this will typically lead to frequent need to reauthenticate and should # # only been enabled if you know what you are doing. # # Note: enabling this will cause `oidc.expiry` to be ignored. # use_expiry_from_token: false # # # Customize the scopes used in the OIDC flow, defaults to "openid", "profile" and "email" and add custom query # # parameters to the Authorize Endpoint request. Scopes default to "openid", "profile" and "email". # # scope: ["openid", "profile", "email", "custom"] # extra_params: # domain_hint: example.com # # # List allowed principal domains and/or users. If an authenticated user's domain is not in this list, the # # authentication request will be rejected. # # allowed_domains: # - example.com # # Note: Groups from keycloak have a leading '/' # allowed_groups: # - /headscale # allowed_users: # - alice@example.com # # # If `strip_email_domain` is set to `true`, the domain part of the username email address will be removed. # # This will transform `first-name.last-name@example.com` to the user `first-name.last-name` # # If `strip_email_domain` is set to `false` the domain part will NOT be removed resulting to the following # user: `first-name.last-name.example.com` # # strip_email_domain: true # Logtail configuration # Logtail is Tailscales logging and auditing infrastructure, it allows the control panel # to instruct tailscale nodes to log their activity to a remote server. logtail: # Enable logtail for this headscales clients. # As there is currently no support for overriding the log server in headscale, this is # disabled by default. Enabling this will make your clients send logs to Tailscale Inc. enabled: false # Enabling this option makes devices prefer a random port for WireGuard traffic over the # default static port 41641. This option is intended as a workaround for some buggy # firewall devices. See https://tailscale.com/kb/1181/firewalls/ for more information. randomize_client_port: true 3、docker-compose 文件 docker这些安装自行搜索
/xxx/headscale/docker-compose.yml
version: '3' services: headscale: image: headscale/headscale:0.22.0 container_name: headscale command: headscale serve sysctls: - net.ipv4.ip_forward=1 - net.ipv6.conf.all.forwarding=1 restart: always volumes: - $PWD/config:/etc/headscale ports: - "21830:8081" - "21831:6030" headscale-ui: image: ghcr.io/gurucomputing/headscale-ui:2023.01.30-beta-1 restart: always container_name: headscale-ui ports: - "21832:80" 4、部署 docker-compose up -d
5、创建 apikey
docker exec headscale headscale api create 6、创建租户 这个自己定义 例如 defname 则下面所有的都替换成defname
docker exec headscale headscale user create <USERNAME> 7、nginx 配置 可同域名,也可不同域名,但是不能默认同ip不同端口,会有跨域问题。
如果是https 使用客户端连接的时候不会自动打开浏览器的,亲测http会自动打开浏览器看到nodekey
server { listen 21833 ssl; # Security / XSS Mitigation Headers server_name localhost; ssl_certificate /usr/share/nginx/8668953_xxxx.xxx.top.pem; ssl_certificate_key /usr/share/nginx/8668953_xxx.xxx-show.top.key; ssl_session_cache shared:SSL:1m; ssl_session_timeout 5m; ssl_ciphers HIGH:!aNULL:!MD5; ssl_prefer_server_ciphers on; add_header X-Frame-Options "SAMEORIGIN"; add_header X-XSS-Protection "1; mode=block"; add_header X-Content-Type-Options "nosniff"; location /web { proxy_redirect off; proxy_set_header Host $host; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_pass http://192.168.123.118:21832; } location / { #proxy_pass http://127.0.0.1:8081; proxy_pass http://192.168.123.118:21830; proxy_http_version 1.1; proxy_set_header Upgrade $http_upgrade; proxy_set_header Connection "upgrade"; proxy_set_header Host $host; proxy_redirect http:// https://; proxy_buffering off; proxy_set_header X-Real-IP $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_set_header X-Forwarded-Proto $http_x_forwarded_proto; add_header Strict-Transport-Security "max-age=15552000; includeSubDomains" always; } } 8、按提示在网页配置域名和apikey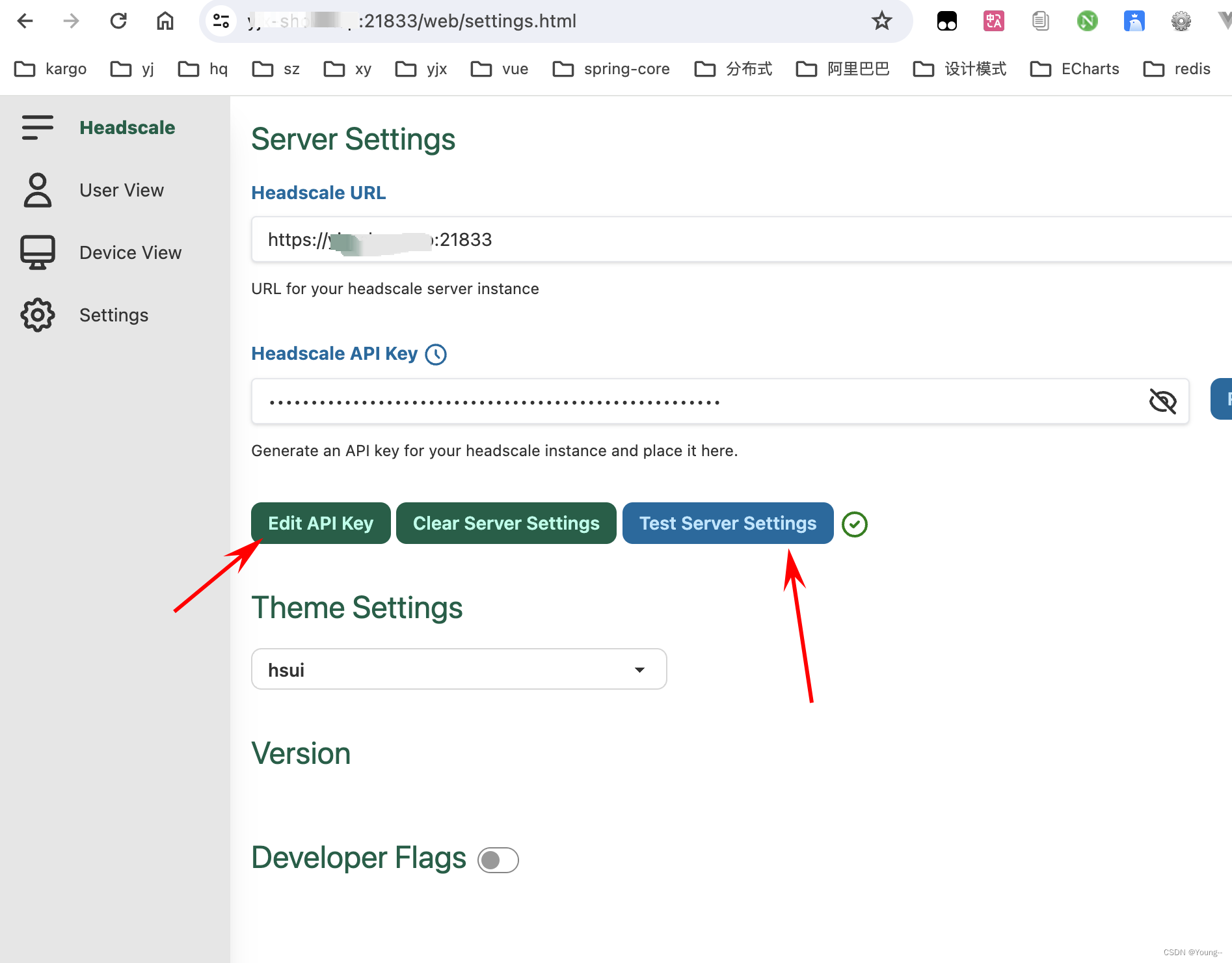
9、客户端安装
9.1、windows:tailscaled 官方下载
安装后执行命令: #如果是第一次登录,注册,192.168.0.0/24改为你局域网ip段 tailscale login --login-server http://服务器ip:21833 #重新登录,ailscale 客户端节点做网关客户端多个子网进行暴露 修改子网路由 多个子网使用逗号分隔 例如 tailscale up --login-server http://ip或者域名:21833 --advertise-exit-node --accept-dns=false --advertise-routes=192.168.0.0/24,192.168.123.0/24 --reset 9.2、linux:
docker 安装:
docker run -d --name tailscaled \ --restart always \ -v /var/lib:/var/lib \ -v /dev/net/tun:/dev/net/tun \ -v /lib/modules:/lib/modules \ --network=host --privileged=true \ tailscale/tailscale tailscaled docker exec -it tailscaled tailscale login --login-server http://<public_ip>:8081 转发配置:
echo 'net.ipv4.ip_forward = 1' | tee /etc/sysctl.d/ipforwarding.conf echo 'net.ipv6.conf.all.forwarding = 1' | tee -a /etc/sysctl.d/ipforwarding.conf sysctl -p 9.3 linux
本地安装
官网:https://tailscale.com/download/linux/static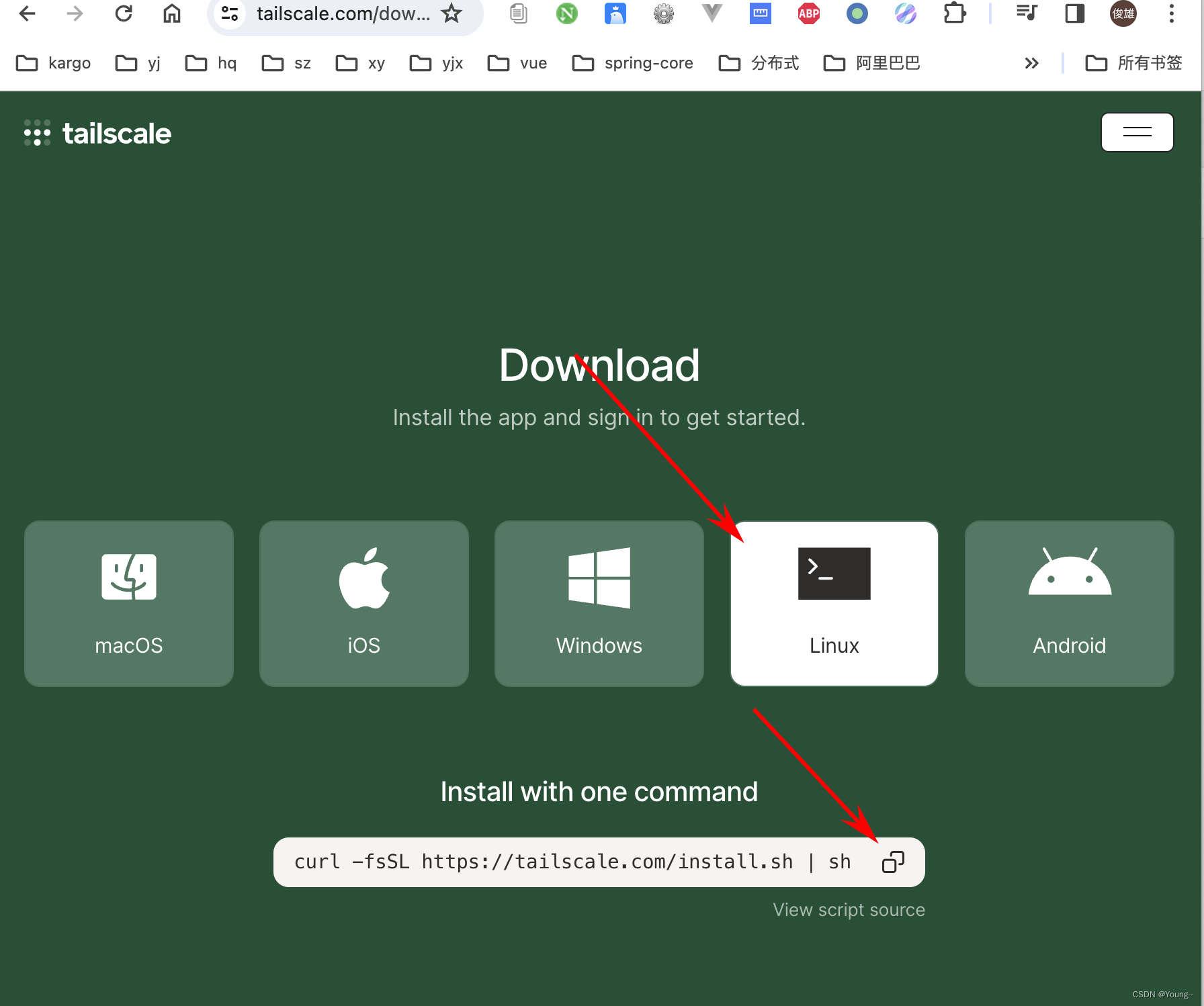
curl -fsSL https://tailscale.com/install.sh | sh #如果是第一次登录,注册,192.168.0.0/24改为你局域网ip段 tailscale login --login-server http://服务器ip:21833 #重新登录,ailscale 客户端节点做网关客户端多个子网进行暴露 修改子网路由 多个子网使用逗号分隔 例如 tailscale up --login-server http://ip或者域名:21833 --advertise-exit-node --accept-dns=false --advertise-routes=192.168.0.0/24,192.168.123.0/24 --reset 执行完成后去看headscale容器日志或者当前窗口日志 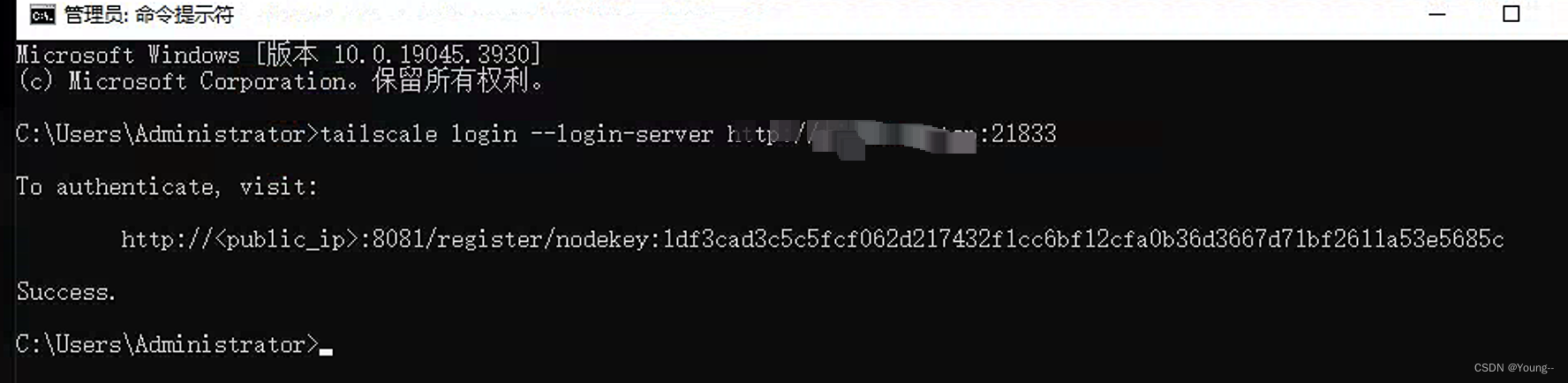
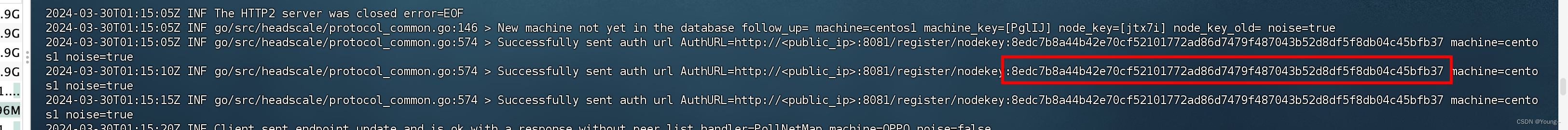
复制出 nodekey:8edc7b8a44b42e70cf52101772ad86d7479f487043b52d8df5f8db04c45bfb37
然后在headscale容器里面执行 下面的命令把linux客户端添加到headscale ,需要修改成自己的用户例如上面的defname
docker exec -it headscale headscale nodes register --user <USERNAME> --key nodekey:a54fcc7eaf88db89d20de099a31e7bcdefeb31e04855fcb75d62d582fd917804 10.安卓app
tailscale.apk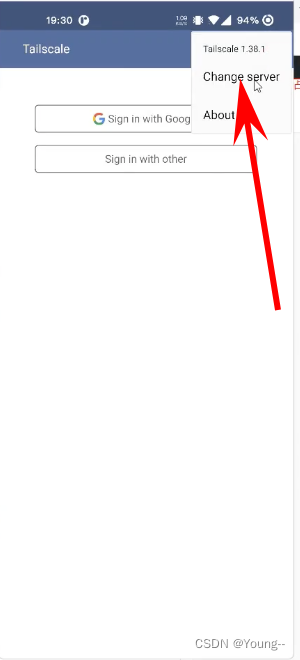
然后填入headscale服务器地址 :和第8步一样,输入https://ip或者域名:21833
输入完成后去 执行完成后去看headscale容器日志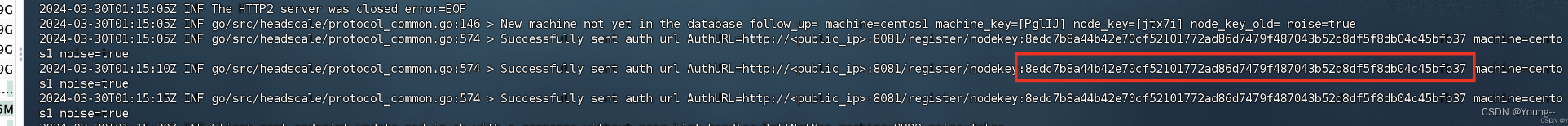
复制出 nodekey:8edc7b8a44b42e70cf52101772ad86d7479f487043b52d8df5f8db04c45bfb37
然后在headscale容器里面执行 下面的命令把linux客户端添加到headscale ,需要修改成自己的用户例如上面的defname
docker exec -it headscale headscale nodes register --user <USERNAME> --key nodekey:a54fcc7eaf88db89d20de099a31e7bcdefeb31e04855fcb75d62d582fd917804 总结, 不管什么客户端连接,都需要去headscale容器看一下连接生成的nodekey,然后执行命令添加客户端
docker exec -it headscale headscale nodes register --user <USERNAME> --key nodekey:a54fcc7eaf88db89d20de099a31e7bcdefeb31e04855fcb75d62d582fd917804 11.macOS
macOS 有 3 种安装方法:
直接通过应用商店安装,地址:https://apps.apple.com/ca/app/tailscale/id1475387142。前提是你需要一个美区 ID。。。
下载安装包直接安装,绕过应用商店。
安装开源的命令行工具 tailscale 和 tailscaled。相关链接:https://github.com/tailscale/tailscale/wiki/Tailscaled-on-macOS。
这三种安装包的核心数据包处理代码是相同的,唯一的区别在于在于打包方式以及与系统的交互方式。
应用商店里的应用运行在一个应用沙箱中,与系统的其他部分隔离。在沙箱内,应用可以是一个网络扩展,以实现 VPN 或者类 VPN 的功能。网络扩展实现的功能对应用商店之外的应用是无法生效的。
从 macOS 从 10.15 开始新增了系统扩展,说白了就是运行在用户态的内核扩展,它相比于传统的网络扩展增强了很多功能,比如内容过滤、透明代理、DNS 代理等。Tailscale 独立于应用商店的安装包使用的就是系统扩展,通过 DMG 或者 zip 压缩包进行分发。
{{< alert >}} 不要同时安装应用商店版本和独立分发版本,同时只能装一个。 {{< /alert >}}
而命令行工具既没有使用网络扩展也没有使用系统扩展,而是使用的 utun 接口,相比于 GUI 版本缺少了部分功能,比如 MagicDNS 和 Taildrop。
直接下载安装包
https://pkgs.tailscale.com/stable/ 可以下来选择安装的版本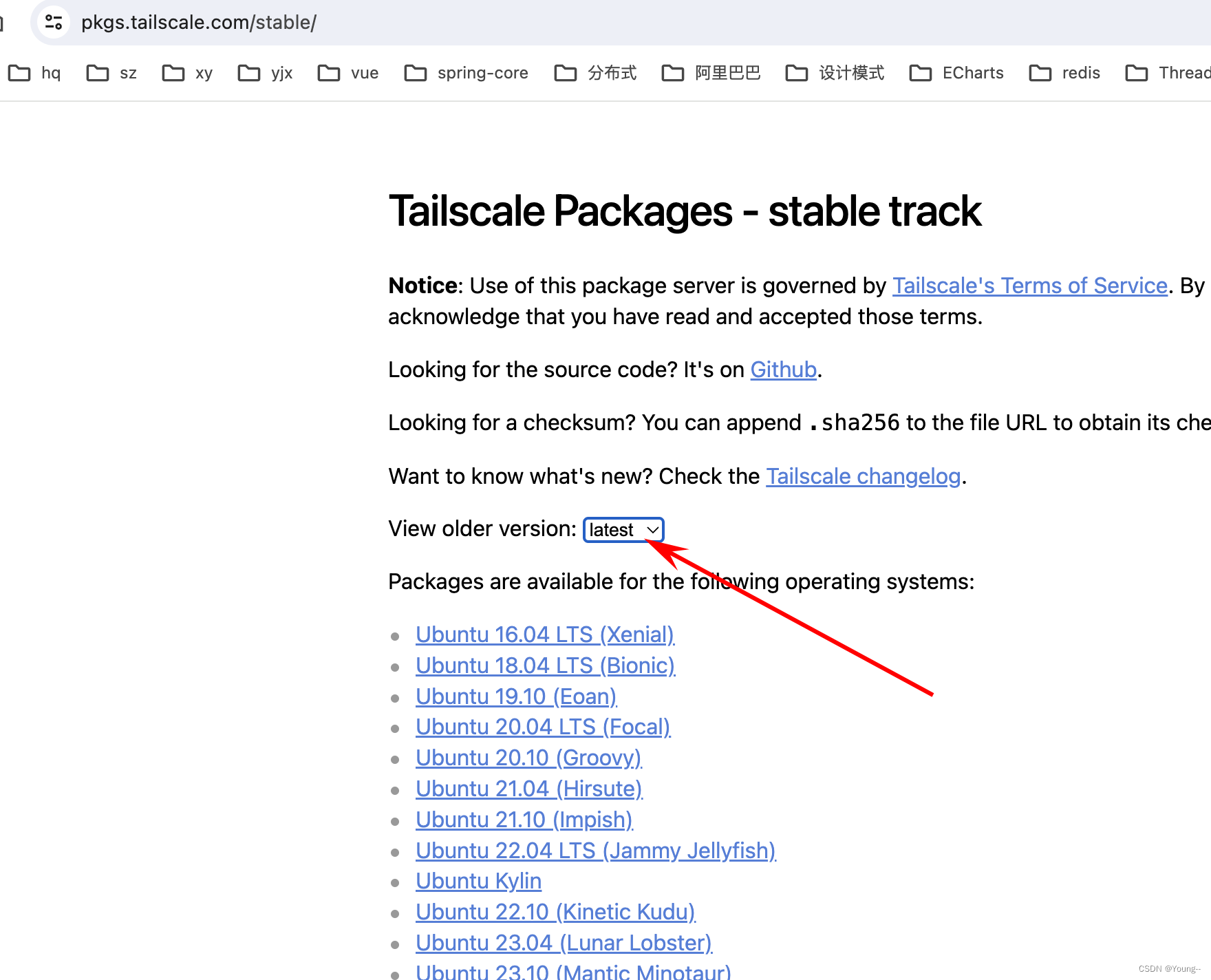
不知道为什么最新版的连接不上自定义headscale服务器
我就使用了1.46.0版本
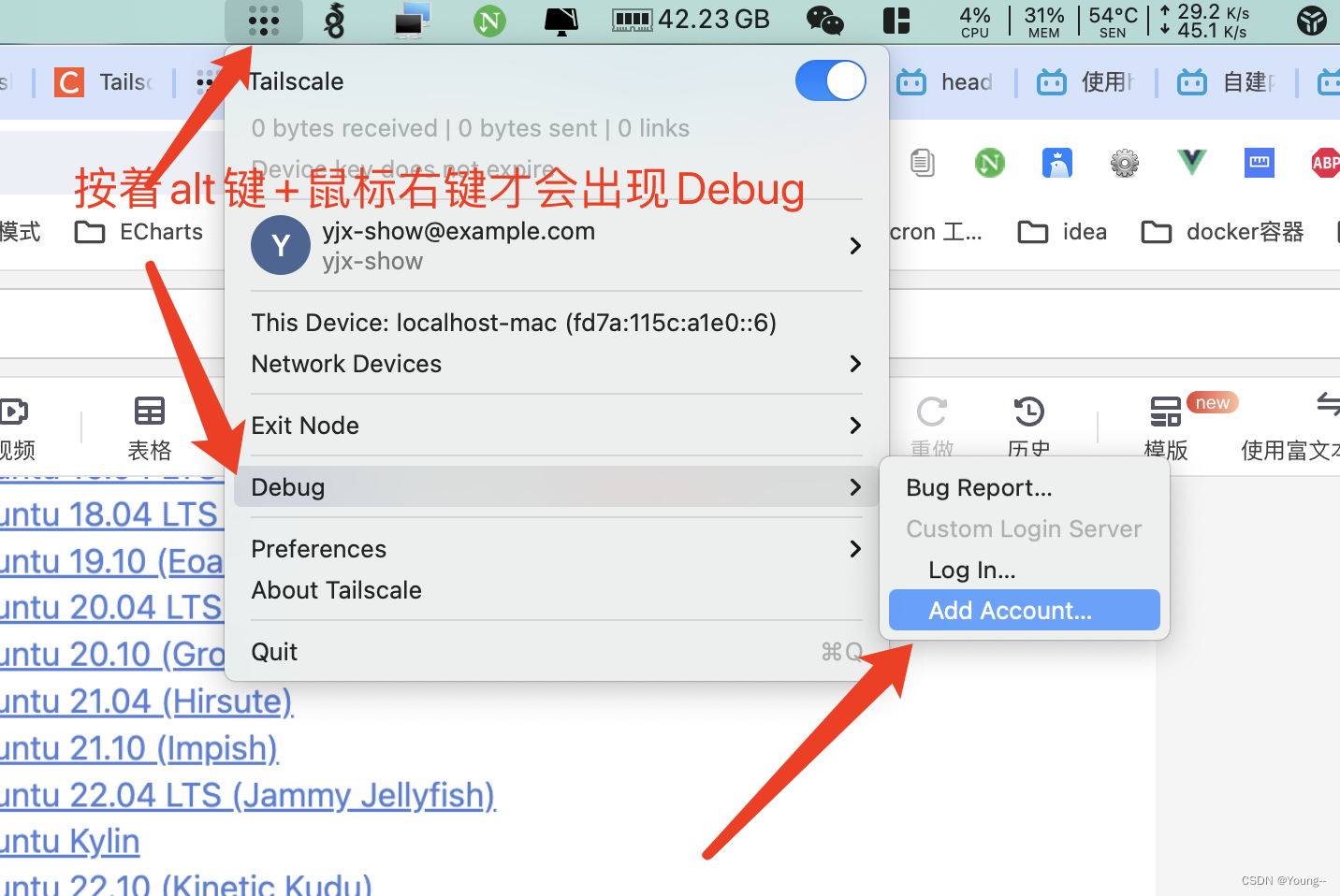
输入headscale服务器后,去headscale容器看nodekey
复制出 nodekey:8edc7b8a44b42e70cf52101772ad86d7479f487043b52d8df5f8db04c45bfb37
然后在headscale容器里面执行 下面的命令把linux客户端添加到headscale ,需要修改成自己的用户例如上面的defname
docker exec -it headscale headscale nodes register --user <USERNAME> --key nodekey:a54fcc7eaf88db89d20de099a31e7bcdefeb31e04855fcb75d62d582fd917804 12 通用 最后一个添加客户端到服务器的 页面简单操作方法
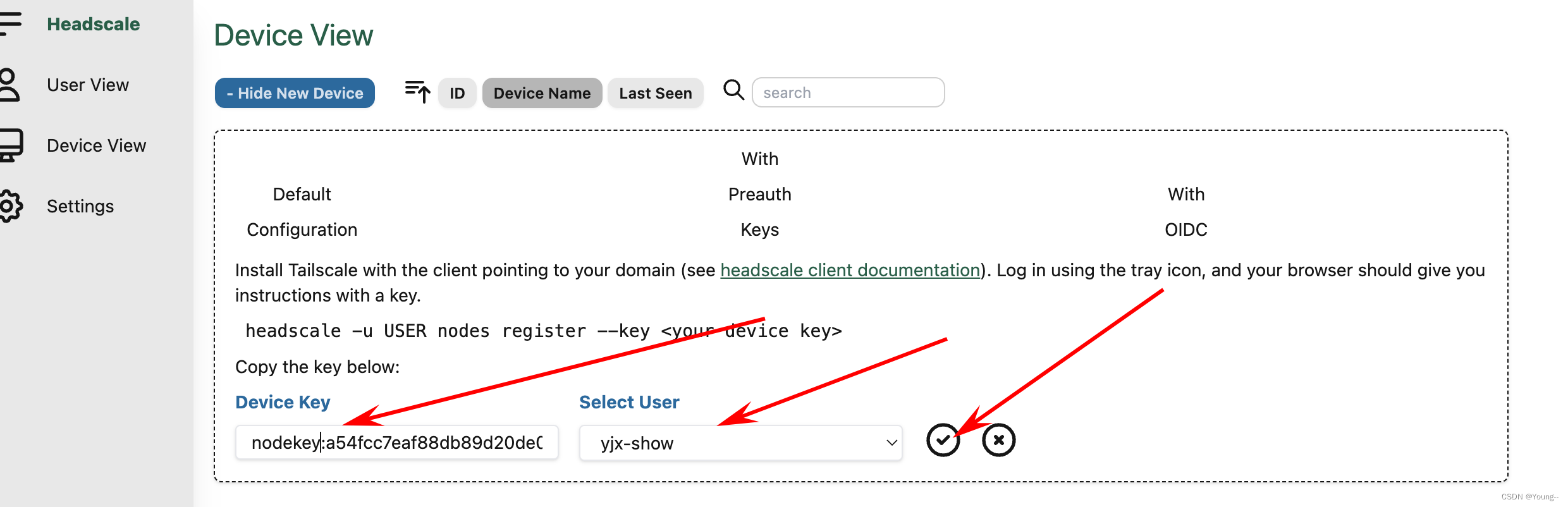
直接复制 nodekey:a54fcc7eaf88db89d20de099a31e7bcdefeb31e04855fcb75d62d582fd917804
https://www.bilibili.com/video/BV1Wh411A73b/?spm_id_from=333.337.search-card.all.click&vd_source=76e331425fd26d8f803c4e03a88ddc41
13、打通局域网,比如家里Windows电脑A,安装了tailscale客户端,外地电脑B,也安装了tailscale客户端,但是家里其他设备比如nas,手机都没有安装tailscale客户端。外地电脑B也可以像家里电脑A一样访问家里局域网内的手机,nas等等设备,就可以用Windows电脑A做路由网关。
就是在外使用任何网络,也可以像在家里一样访问家里局域网内的手机,电脑,nas,路由等等。
只需要修改一下注册登录命令即可,后面服务器验证都是一样的。
家里Windows电脑A:
#如果是第一次登录,注册,192.168.0.0/24改为你局域网ip段 tailscale login --login-server http://服务器ip:21833 #重新登录,ailscale 客户端节点做网关客户端多个子网进行暴露 修改子网路由 多个子网使用逗号分隔 例如 tailscale up --login-server http://ip或者域名:21833 --advertise-exit-node --accept-dns=false --advertise-routes=192.168.0.0/24,192.168.123.0/24 --reset 如果家里是linux电脑,或者openwrt等软路由:
上面也是一样的,只是多一个端口转发:
echo 'net.ipv4.ip_forward = 1' | tee /etc/sysctl.d/ipforwarding.conf echo 'net.ipv6.conf.all.forwarding = 1' | tee -a /etc/sysctl.d/ipforwarding.conf sysctl -p /etc/sysctl.d/ipforwarding.conf headtail服务端添加一下路由即可:
#查看路由列表,获取需要打通的局域网序号
headscale routes list #比如打通序号1的路由
headscale routes enable -r 1 - tailscale 客户端节点做网关客户端多个子网进行暴露 修改子网路由 多个子网使用逗号分隔 例如10.100.70.0/24,10.100.71.0/24
tailscale up --login-server http://ip或者域名:21833 --advertise-exit-node --accept-dns=false --advertise-routes=192.168.0.0/24,192.168.123.0/24 --reset 14,一些补充功能
14.1
删除节点或子网关
headscale routes list headscale routes enable -r 1 //1为 routes list 的id headscale routes disable -r 1 //禁用路由 headscale routes delete -r 1 //删除路由 namespace
headscale namespace list # 查看所有的namespace headscale namespace create default # 创建namespace headscale namespace destroy default # 删除namespace headscale namespace rename default myspace # 重命名namespace node
headscale node list # 列出所有的节点 headscale node ls -t # 列出所有的节点,同时显示出tag信息 headscale -n default node ls # 只查看namespace为default下的节点 headscale node delete -i<ID> # 根据id删除指定的节点,这里面的id是node list查询出来的id # 参考headscale nodes delete -i=6 headscale node tag -i=2 -t=tag:test # 给id为2的node设置tag为tag:test route
