阅读量:1
问题描述:
今日在工作中遇到服务器被扫描出一个漏洞,描述如下:
风险描述:远程 Web 服务器支持 TRACE 和/或 TRACK方法。TRACE和 TRACK 是用于调试 Web 服务器连接的 HTTP 方法。
风险影响:通过一个跨站追踪攻击窃职 cookies 和验证信任
使用框架
springboot + redis +mybatis
web服务使用springboot 内嵌web服务 undertow
配置如下:
<!-- SpringBoot Web容器 --> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-web</artifactId> <exclusions> <exclusion> <artifactId>spring-boot-starter-tomcat</artifactId> <groupId>org.springframework.boot</groupId> </exclusion> </exclusions> </dependency> <!-- web 容器使用 undertow 性能更强 --> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-undertow</artifactId> </dependency> <dependency> <groupId>io.undertow</groupId> <artifactId>undertow-servlet</artifactId> </dependency> 在网上找啊找啊,大多是tomcat的,终于找到一个
@Bean public UndertowEmbeddedServletContainerFactory embeddedServletContainerFactory() { UndertowEmbeddedServletContainerFactory factory = new UndertowEmbeddedServletContainerFactory(); factory.addBuilderCustomizers(new UndertowBuilderCustomizer() { @Override public void customize(Builder builder) { builder.addHttpListener(8080, "0.0.0.0"); } }); return factory; } 很遗憾不能用,各种类找不到BUG,接续找,终于找到springboot 2.0之后类名字变更,所以修改如下:
package com.ruoyi.medicine.config; import io.undertow.servlet.api.DeploymentInfo; import io.undertow.servlet.api.SecurityConstraint; import io.undertow.servlet.api.WebResourceCollection; import org.springframework.boot.web.embedded.undertow.UndertowDeploymentInfoCustomizer; import org.springframework.boot.web.embedded.undertow.UndertowServletWebServerFactory; import org.springframework.boot.web.server.WebServerFactory; import org.springframework.boot.web.server.WebServerFactoryCustomizer; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; import org.springframework.http.HttpMethod; /** * @author wang'hai'yang * @Description: * @date 2024/2/2110:46 */ @Configuration public class EmbeddedServletContainerCustomizerConfig { @Bean public WebServerFactoryCustomizer containerCustomizer() { return new WebServerFactoryCustomizer() { @Override public void customize(WebServerFactory factory) { if(factory.getClass().isAssignableFrom(UndertowServletWebServerFactory.class)){ UndertowServletWebServerFactory underTowContainer = (UndertowServletWebServerFactory) factory; underTowContainer.addDeploymentInfoCustomizers(new ContextSecurityCustomizer()); } } }; } private static class ContextSecurityCustomizer implements UndertowDeploymentInfoCustomizer { @Override public void customize(DeploymentInfo deploymentInfo) { SecurityConstraint constraint = new SecurityConstraint(); WebResourceCollection traceWebresource = new WebResourceCollection(); traceWebresource.addUrlPattern("/*"); traceWebresource.addHttpMethod(HttpMethod.TRACE.toString()); constraint.addWebResourceCollection(traceWebresource); deploymentInfo.addSecurityConstraint(constraint); } } } 测试方式及结果
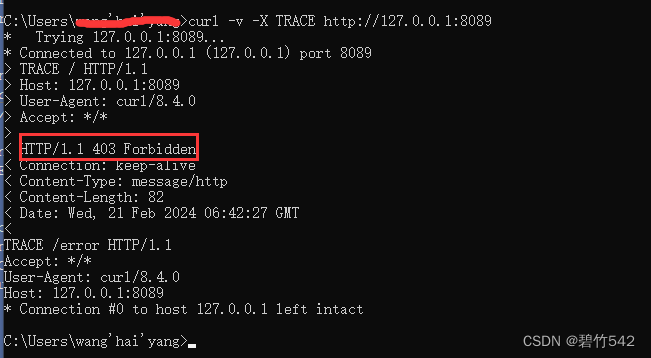
如图所示,代表成功,否则 红框所示地方显示 HTTP/1.1 200 OK
