需求
实验
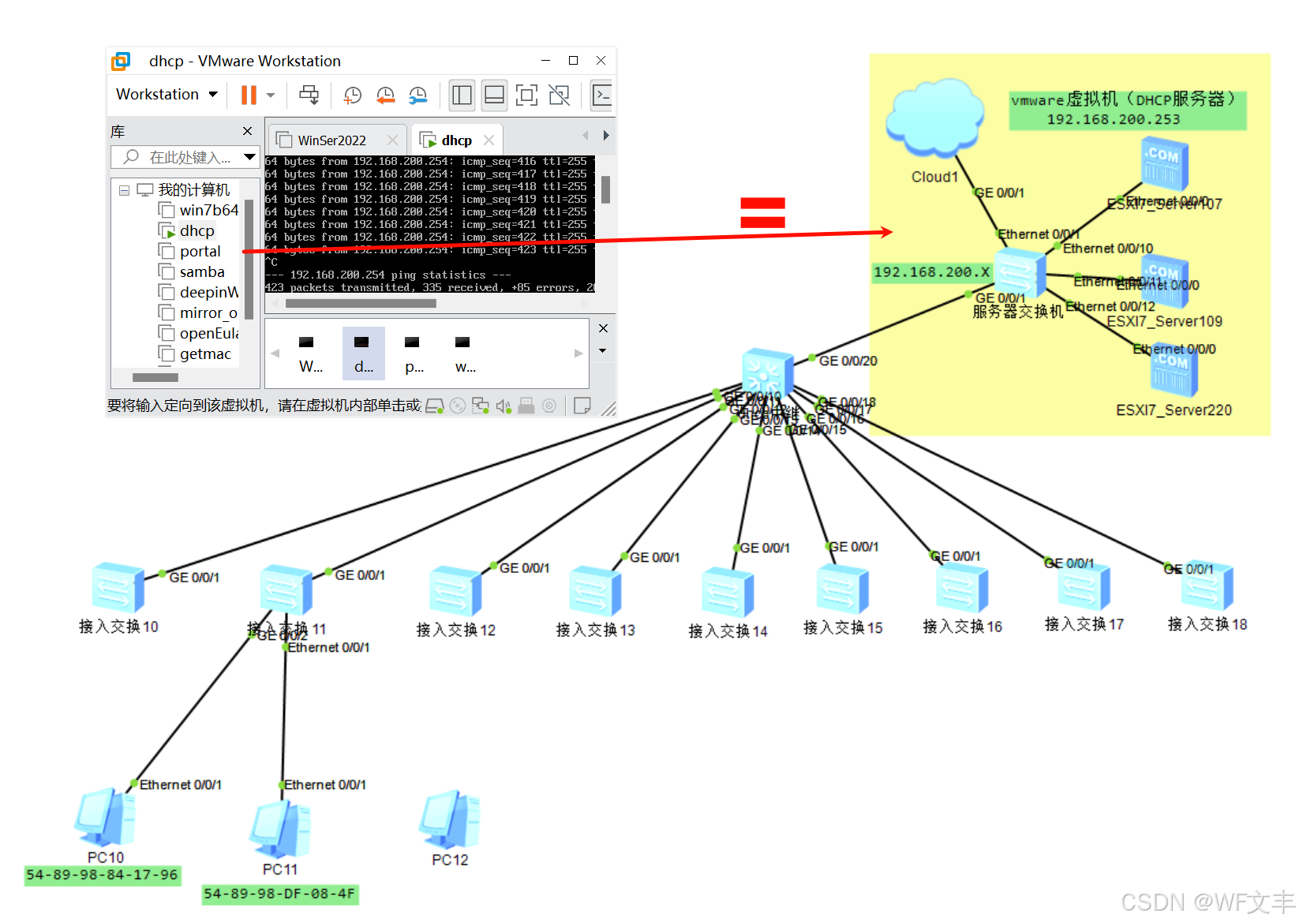
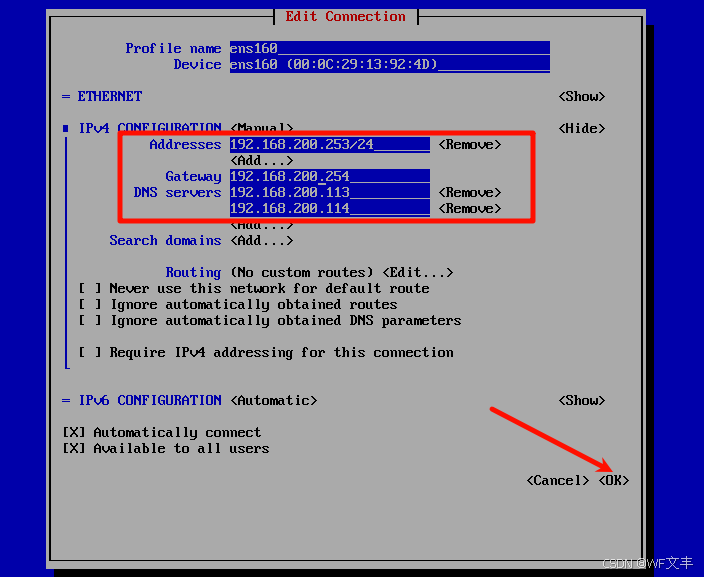
vmware网络配置(企业内部一般为ESXI)
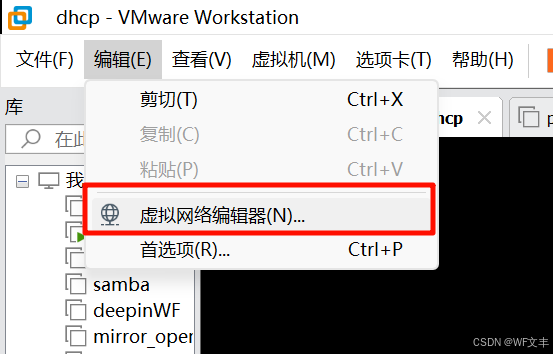

这样服务器虚拟机使用192.168.200.X网段才能与用户侧互通
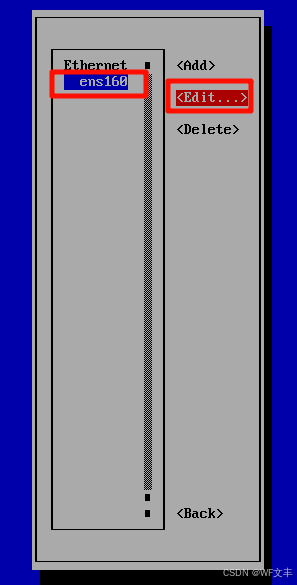
vmware虚拟机配置(DHCP服务器网络配置)
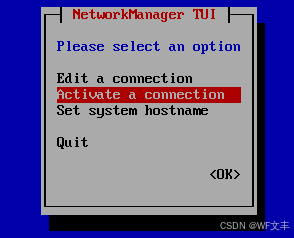
- 打开网络管理页面
nmtui 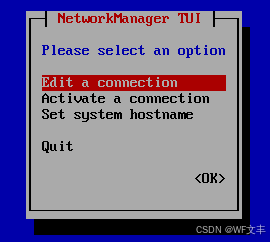
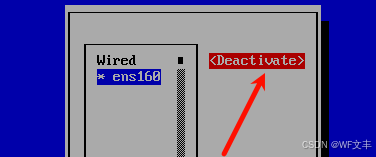
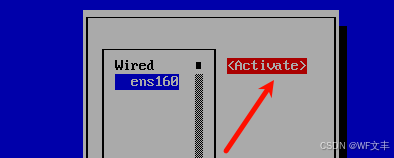
重置一下网络连接(重启网卡)
检查IP地址
ip addr 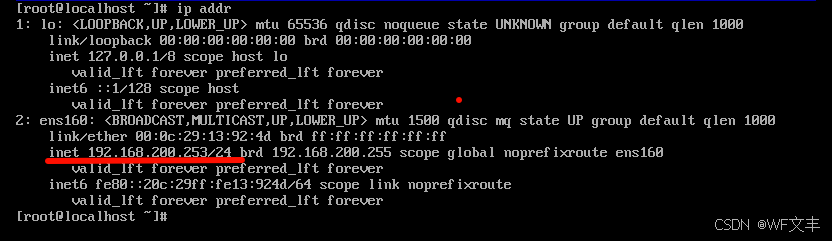
清空交换机所有配置信息并重启
# quit reset saved-configuration reboot 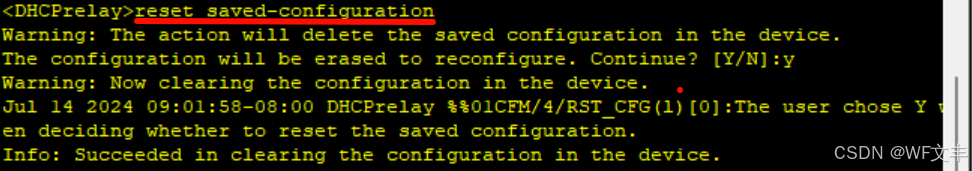
中继交换机(核心交换机)网络配置
- 根据规划,划分vlan 10-18、20、200
# sysname DHCPrelay vlan batch 10 to 18 20 200 - 配置vlan接口地址(网关)
# int vlanif 10 ip add 192.168.10.254 24 # int vlanif 11 ip add 192.168.11.254 24 # int vlanif 12 ip add 192.168.12.254 24 # int vlanif 13 ip add 192.168.13.254 24 # int vlanif 14 ip add 192.168.14.254 24 # int vlanif 15 ip add 192.168.15.254 24 # int vlanif 16 ip add 192.168.16.254 24 # int vlanif 17 ip add 192.168.17.254 24 # int vlanif 18 ip add 192.168.18.254 24 # int vlanif 20 ip add 192.168.20.254 24 # int vlanif 200 ip add 192.168.200.254 24 接口通联性配置及ping测试
# int g 0/0/20 port link-type hybrid port hybrid pvid vlan 200 port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/10 mac-vlan enable port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/11 mac-vlan enable port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/12 port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/13 port link-type hybrid port hybrid tagged vlan 10 to 18 20 200 # int g 0/0/14 port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/15 port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/16 port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 # int g 0/0/17 port link-type hybrid port hybrid tagged vlan 10 to 18 20 200 # int g 0/0/18 port link-type hybrid port hybrid untagged vlan 10 to 18 20 200 在服务器交接机e 0/0/1处抓包
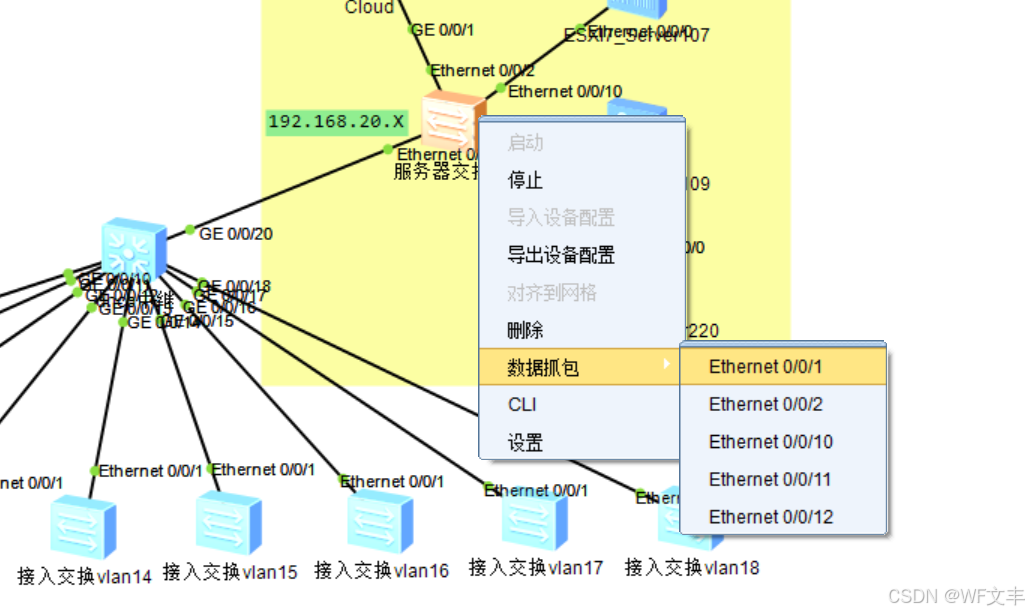
发现PC10 的DHCP广播报文已到达此接口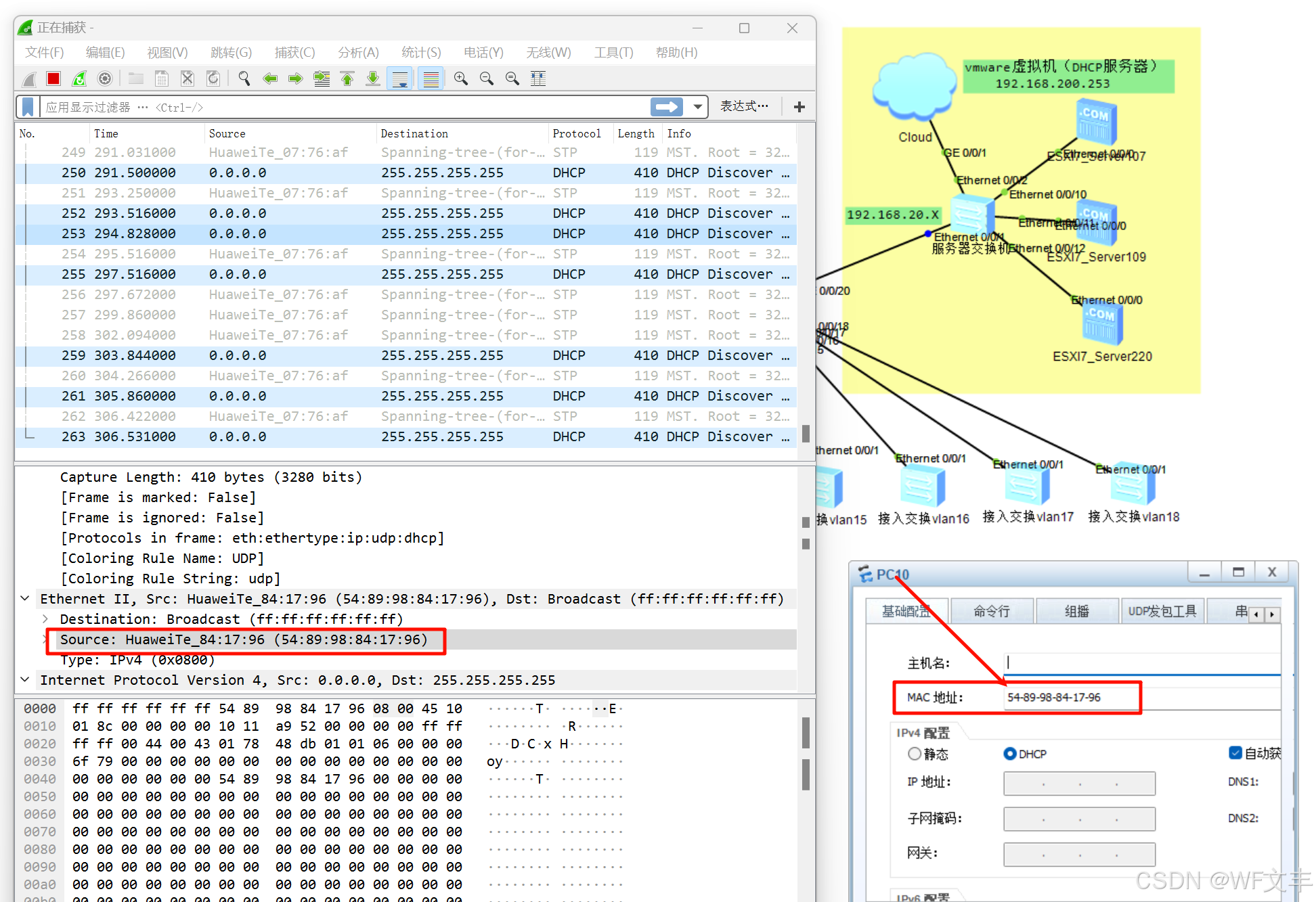
ping命令测试(给PC10手动设置IP 192.168.10.99)
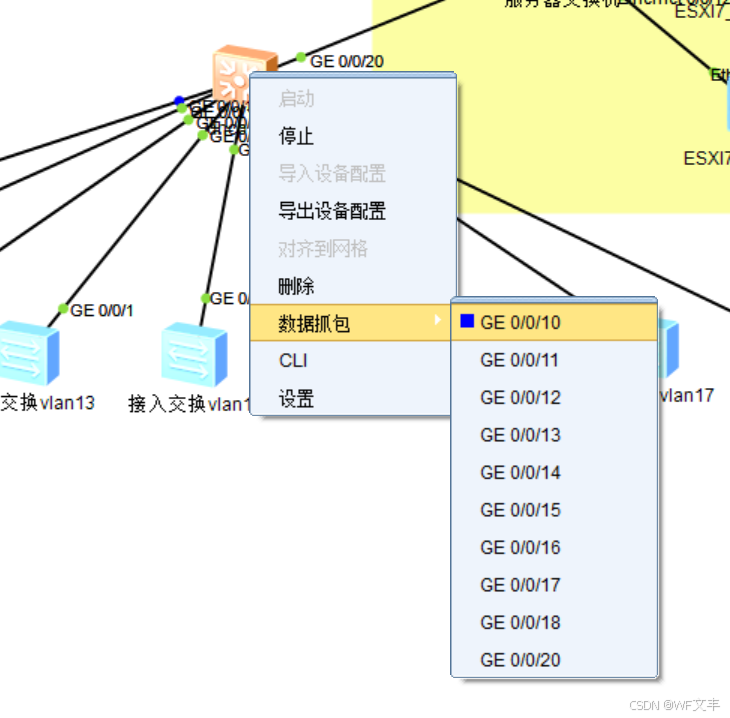
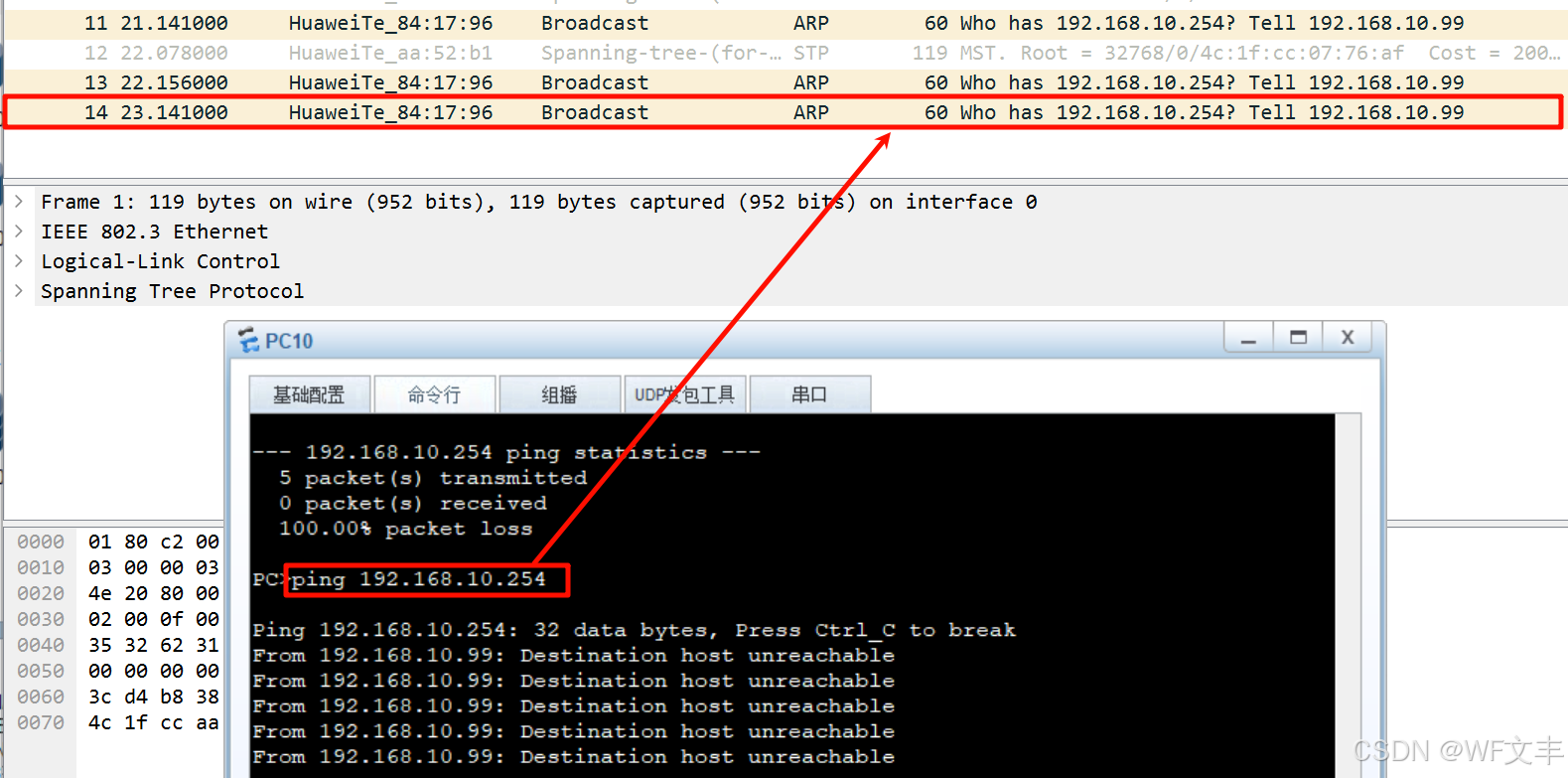
以上可以看出只有 ARP报文,报文无法到达192.168.10.254(中继交换机vlanif 10 接口地址)再次用ping命令测试(给PC10手动设置IP 192.168.10.99)
测试前,配置mac-vlan
# vlan 10 mac-vlan mac-address 5489-9884-1796 # int g 0/0/10 mac-vlan enable 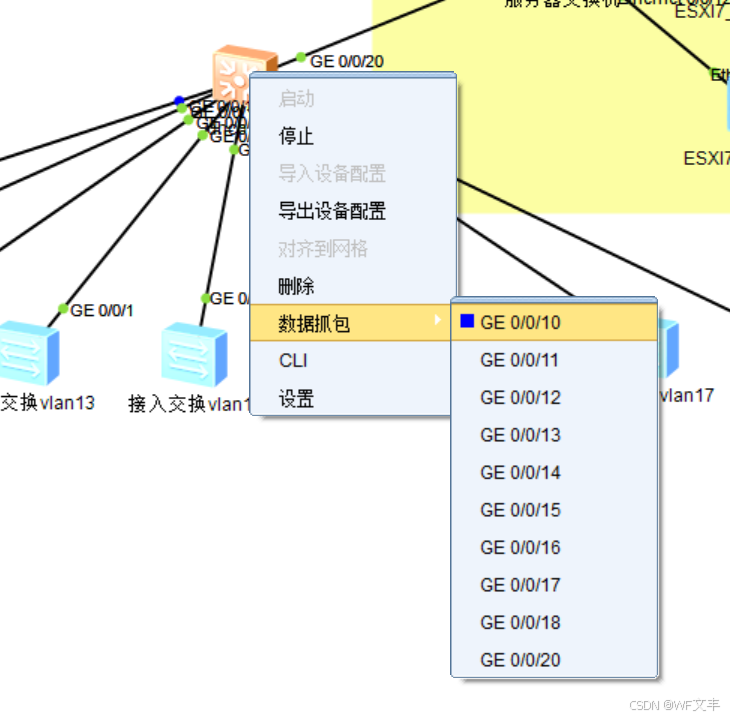
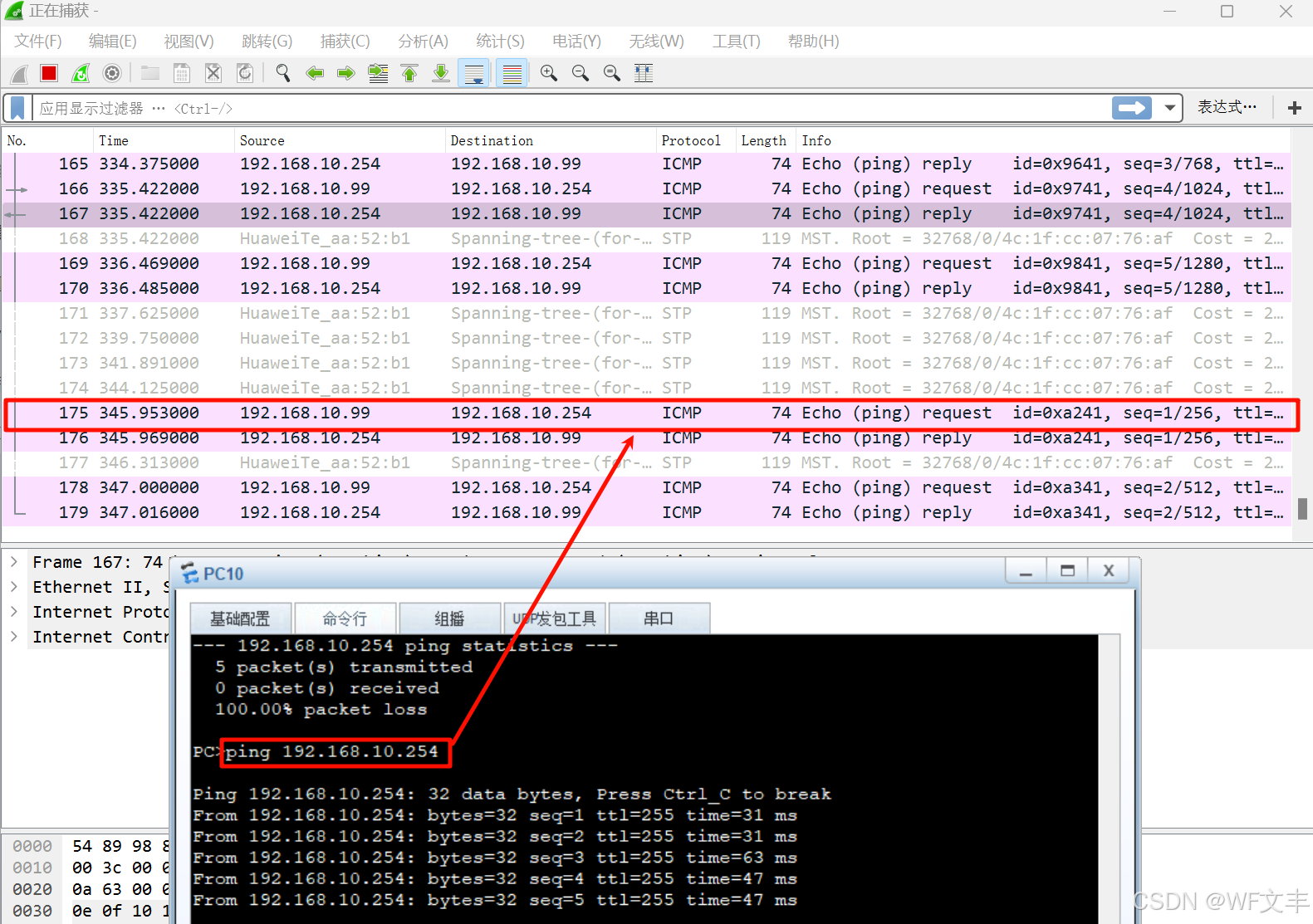
正常通信
配置DHCP中继
# int vlanif 10 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 11 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 12 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 13 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 14 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 15 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 16 dhcp select relay dhcp relay server-ip 192.168.200.253 # int vlanif 17 dhcp select relay dhcp relay server-ip 192.168.200.253 quit # int vlanif 18 dhcp select relay dhcp relay server-ip 192.168.200.253 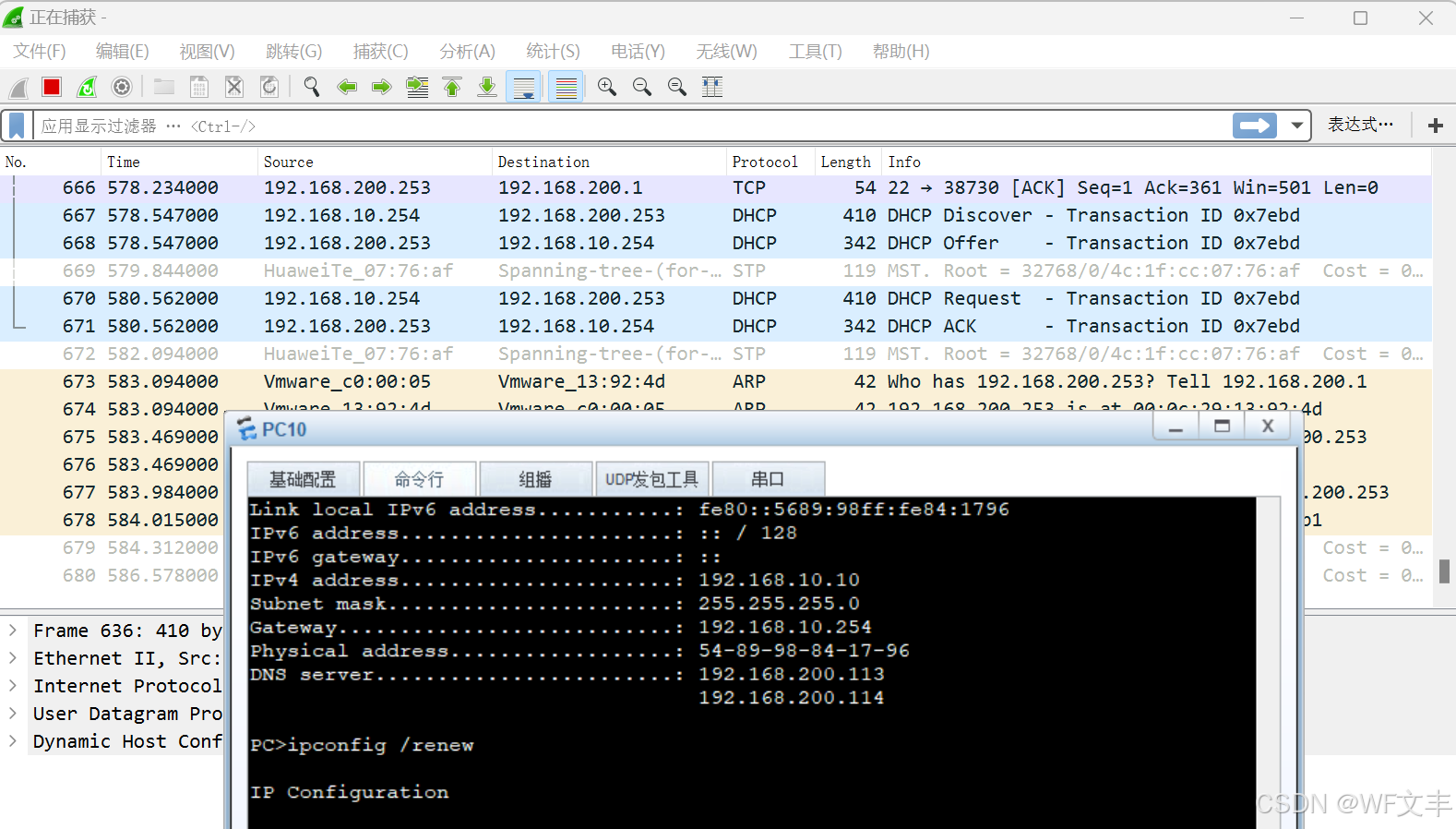
PC10正常获取IP
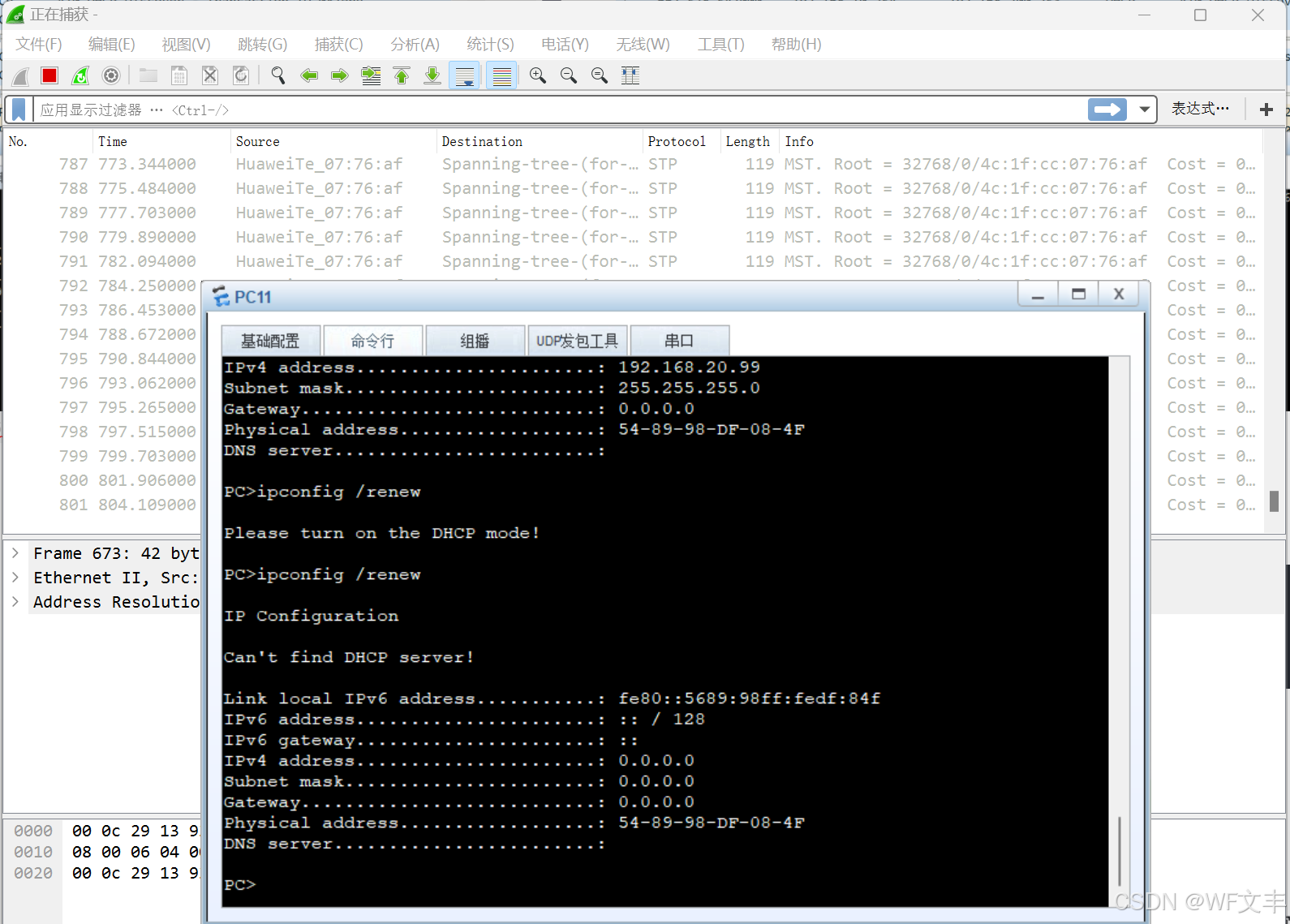
PC11无法正常获取IP(因为DHCP中继是做在vlanif接口上的,而PC11无确定Vlan)
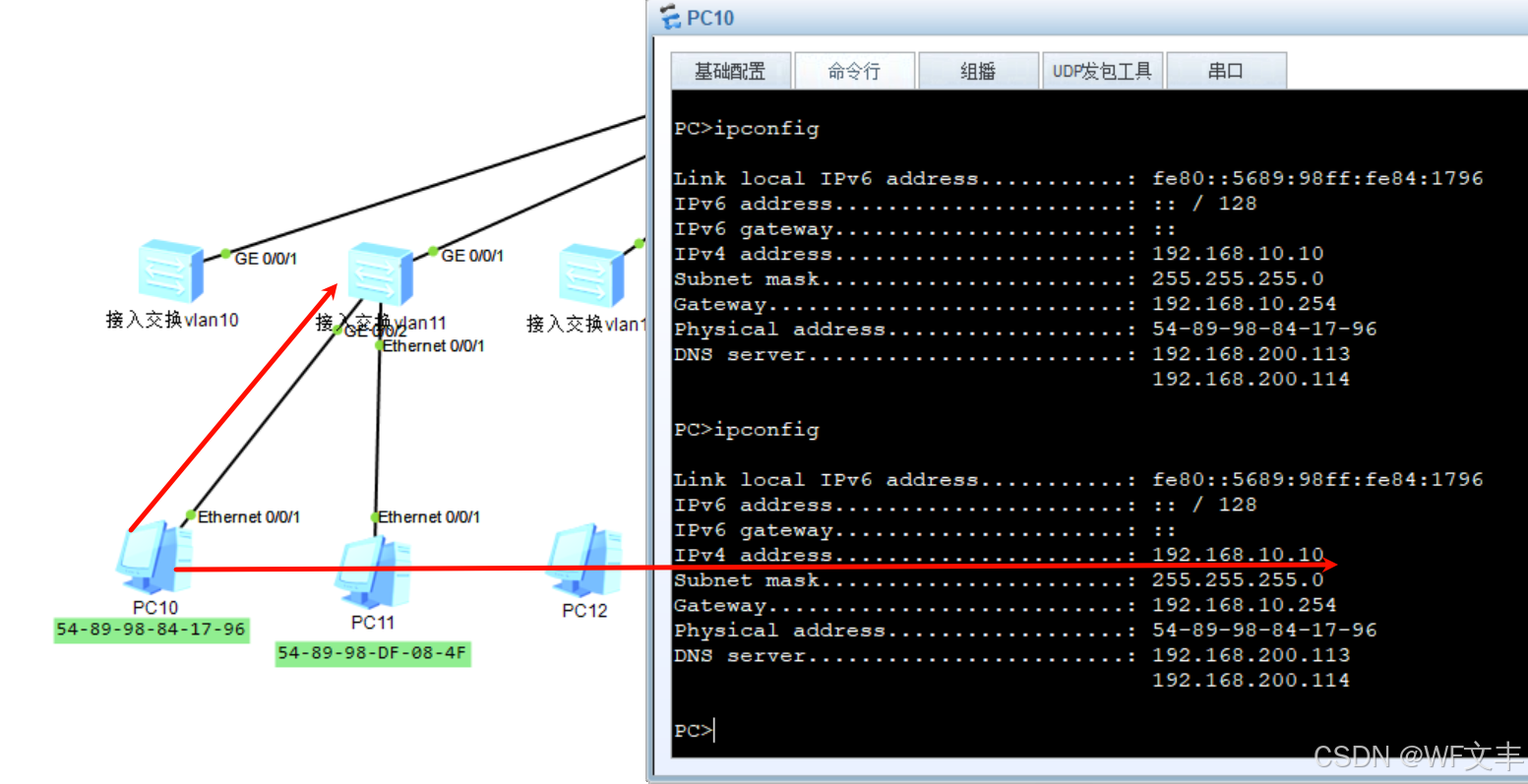
把PC10接入vlan11 的交接机获取的IP依然是vlan10 (MAC-Vlan)
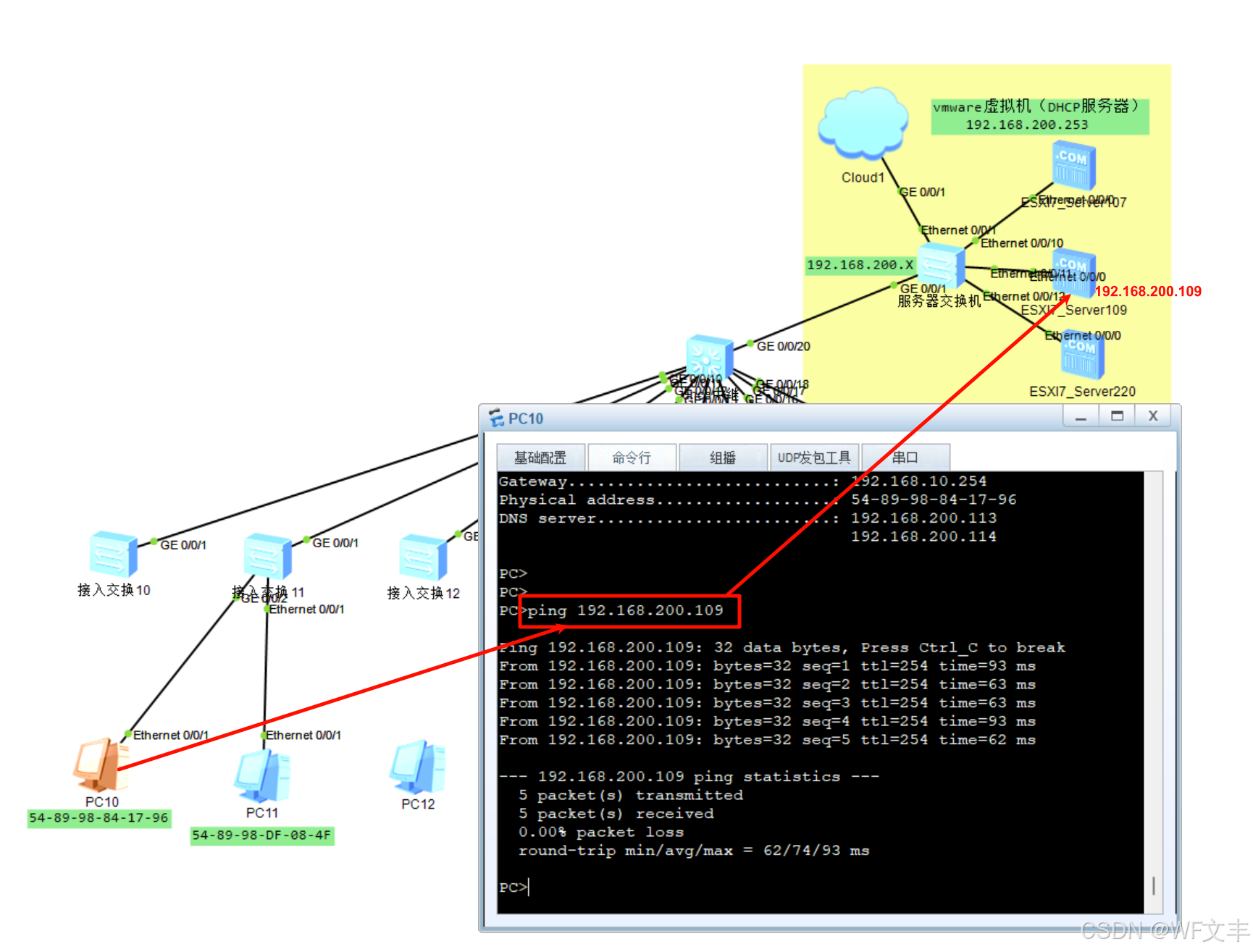 与服务器正常通信
与服务器正常通信
配置mac-vlan
# vlan 10 # int g 0/0/10 mac-vlan enable # vlan 11 # int g 0/0/11 mac-vlan enable # vlan 12 # int g 0/0/12 mac-vlan enable # vlan 13 # int g 0/0/13 mac-vlan enable # vlan 14 # int g 0/0/14 mac-vlan enable # vlan 15 # int g 0/0/15 mac-vlan enable # vlan 16 # int g 0/0/16 mac-vlan enable # vlan 17 # int g 0/0/17 mac-vlan enable # vlan 18 # int g 0/0/12 mac-vlan enable # vlan 18 # int g 0/0/12 mac-vlan enable 配置dhcp-snooping、ip source check
# dhcp enable # dhcp snooping enable # int g 0/0/20 dhcp snooping enable dhcp snooping trusted # int g 0/0/10 dhcp snooping enable # int g 0/0/11 dhcp snooping enable # int g 0/0/12 dhcp snooping enable # int g 0/0/13 dhcp snooping enable # int g 0/0/14 dhcp snooping enable # int g 0/0/15 dhcp snooping enable # int g 0/0/16 dhcp snooping enable # int g 0/0/17 dhcp snooping enable # int g 0/0/18 dhcp snooping enable 配置ip source check(禁手动修改IP)
# int g 0/0/10 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/11 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/12 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/13 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/14 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/15 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/16 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/17 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable # int g 0/0/18 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping check dhcp-chaddr enable 交换机配置文件如下
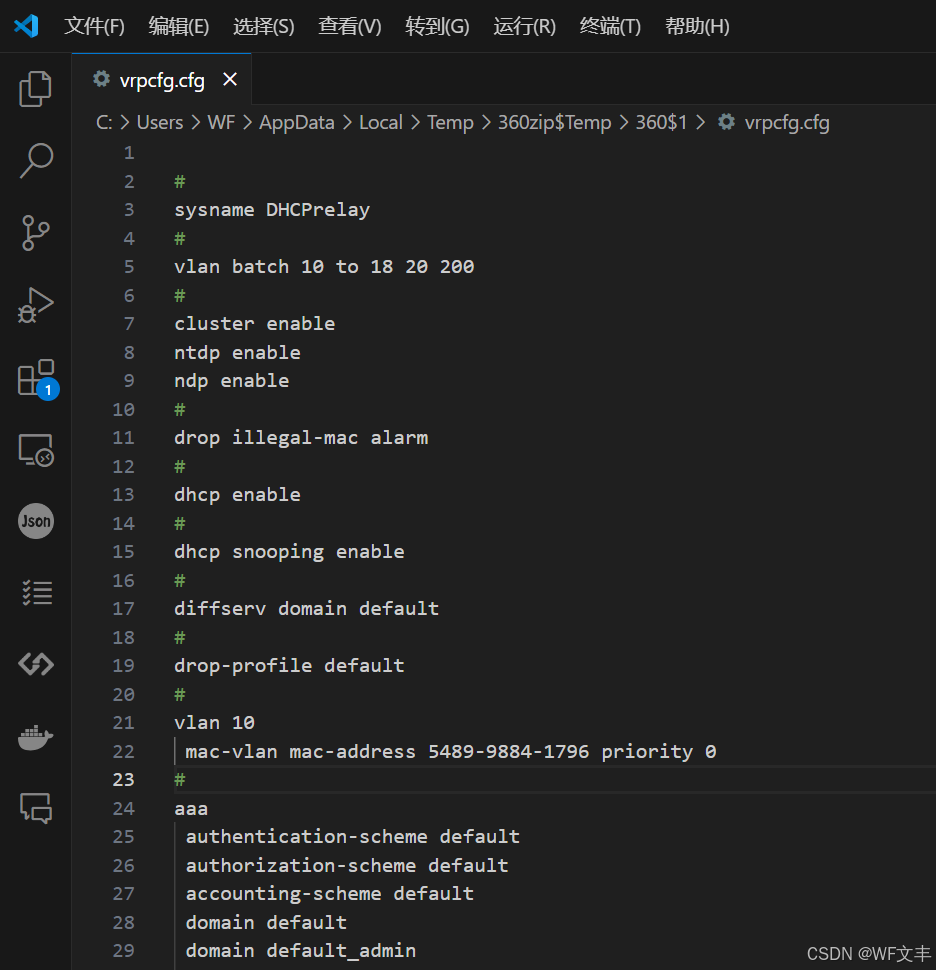
# sysname DHCPrelay # FTP server enable # vlan batch 10 to 18 20 200 # cluster enable ntdp enable ndp enable # drop illegal-mac alarm # dhcp enable # dhcp snooping enable # diffserv domain default # drop-profile default # vlan 10 mac-vlan mac-address 5489-9884-1796 priority 0 # aaa authentication-scheme default authorization-scheme default accounting-scheme default domain default domain default_admin local-user admin password cipher '!7<XEEUSW1-R^[64VOP.A!! local-user admin privilege level 15 local-user admin ftp-directory flash:/ local-user admin service-type ftp # interface Vlanif1 # interface Vlanif10 ip address 192.168.10.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif11 ip address 192.168.11.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif12 ip address 192.168.12.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif13 ip address 192.168.13.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif14 ip address 192.168.14.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif15 ip address 192.168.15.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif16 ip address 192.168.16.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif17 ip address 192.168.17.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif18 ip address 192.168.18.254 255.255.255.0 dhcp select relay dhcp relay server-ip 192.168.200.253 # interface Vlanif20 ip address 192.168.20.254 255.255.255.0 # interface Vlanif200 ip address 192.168.200.254 255.255.255.0 # interface MEth0/0/1 # interface GigabitEthernet0/0/1 # interface GigabitEthernet0/0/2 # interface GigabitEthernet0/0/3 # interface GigabitEthernet0/0/4 # interface GigabitEthernet0/0/5 # interface GigabitEthernet0/0/6 # interface GigabitEthernet0/0/7 # interface GigabitEthernet0/0/8 # interface GigabitEthernet0/0/9 # interface GigabitEthernet0/0/10 port hybrid untagged vlan 10 to 18 20 200 mac-vlan enable arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/11 port hybrid untagged vlan 10 to 18 20 200 mac-vlan enable arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/12 port hybrid untagged vlan 10 to 18 20 200 mac-vlan enable arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/13 port hybrid tagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/14 port hybrid untagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/15 port hybrid untagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/16 port hybrid untagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/17 port hybrid tagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/18 port hybrid untagged vlan 10 to 18 20 200 arp anti-attack check user-bind enable ip source check user-bind enable dhcp snooping enable dhcp snooping check dhcp-chaddr enable # interface GigabitEthernet0/0/19 # interface GigabitEthernet0/0/20 port hybrid pvid vlan 200 port hybrid untagged vlan 10 to 18 20 200 dhcp snooping enable dhcp snooping trusted # interface GigabitEthernet0/0/21 # interface GigabitEthernet0/0/22 # interface GigabitEthernet0/0/23 # interface GigabitEthernet0/0/24 # interface NULL0 # sftp server enable stelnet server enable ssh user admin ssh user admin authentication-type password ssh user admin service-type sftp ssh user admin sftp-directory flash:/ # user-interface con 0 user-interface vty 0 4 authentication-mode aaa protocol inbound ssh # return ssh与sftp配置
相关解释请访问:
- https://blog.csdn.net/xzzteach/article/details/140419150
- https://blog.csdn.net/xzzteach/article/details/140420985
开户stelnet权限
# stelnet server enable 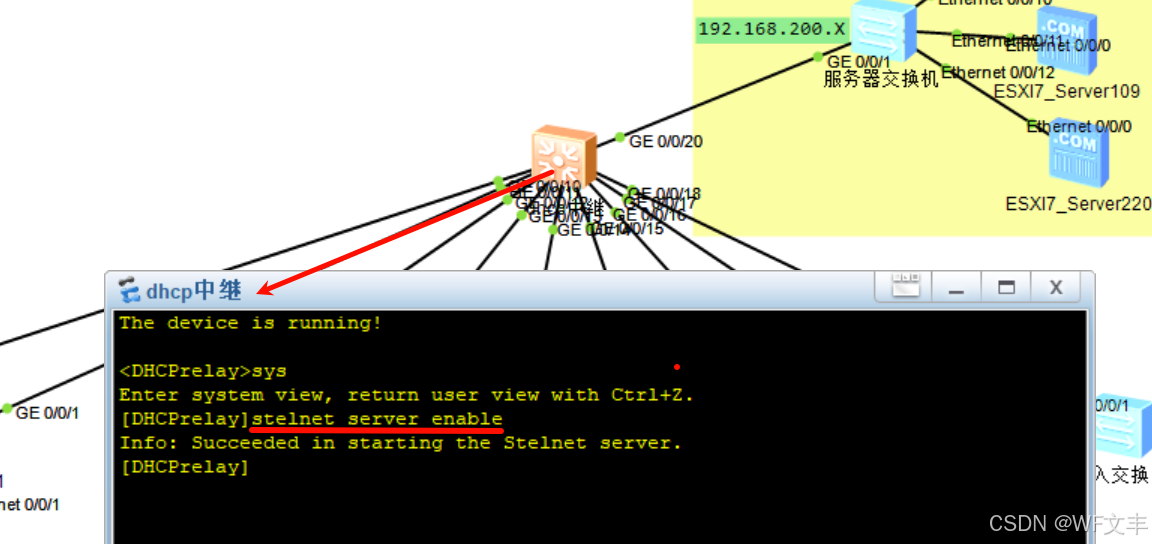
创建本地密钥对
# rsa local-key-pair create 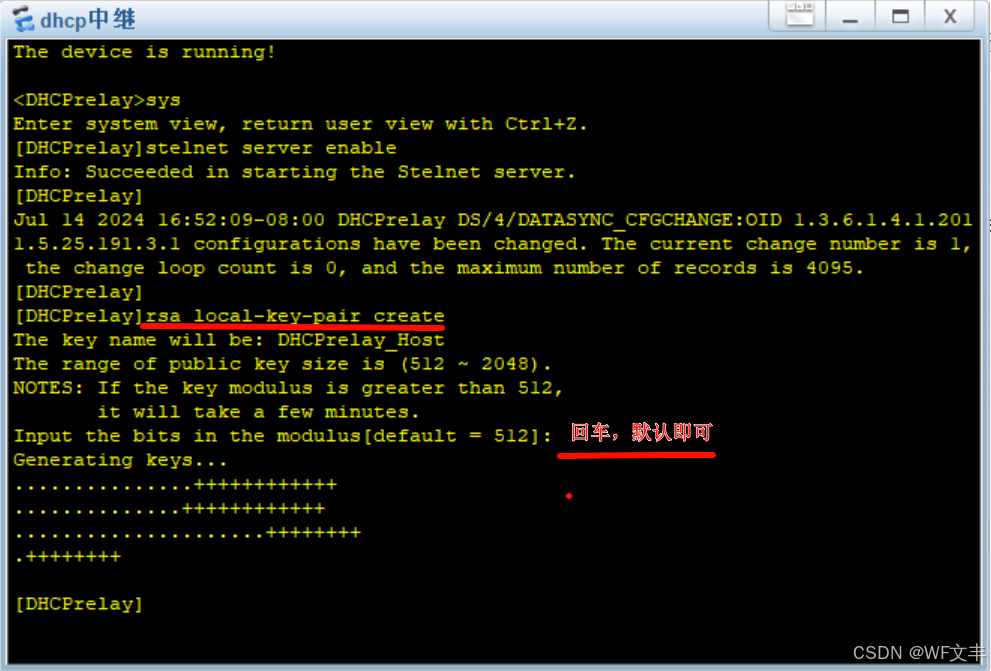
创建ssh用户名为admin
- 创建用户admin
- 创建用户认证为密码认证
- 服务类型为ssh
# ssh user admin ssh user admin authentication-type password ssh user admin service-type stelnet ssh user admin service-type sftp aaa模式下配置用户
- 进入aaa模式
- 配置用户密码为openEuler@2021
- 配置用户权限级别(级别15通常允许用户执行所有命令,包括可能影响设备配置和运行的敏感或高级命令)
- 允许用户ssh访问权限
# aaa local-user admin password cipher openEuler@2021 local-user admin privilege level 15 local-user admin service-type ssh 配置vty界面支持的登录协议
- 进入vty 0 4
- 认证为aaa
- 登录协议为ssh登入
# user-interface vty 0 4 authentication-mode aaa protocol inbound ssh 核心交接机全部配置-备份还原
华为交换机备份配置文件和还原配置文件的方法有多种,以下是一些常见的方法:
备份配置文件
使用命令行界面:
通过display current-configuration命令查看当前配置。
将显示的信息拷贝到一个TXT文本文件中,从而备份配置文件到维护终端的硬盘中。
需要注意的是,如果现实界面中有换行的命令,需要删除换行,否则当使用制作的TXT文本恢复配置时,换行的配置将无法恢复。
使用图形用户界面(GUI):
打开GUI,登录到交换机的管理界面1。
导航到配置管理页面1。
选择要保存的配置文件,并点击保存按钮,将配置保存到指定的位置1。
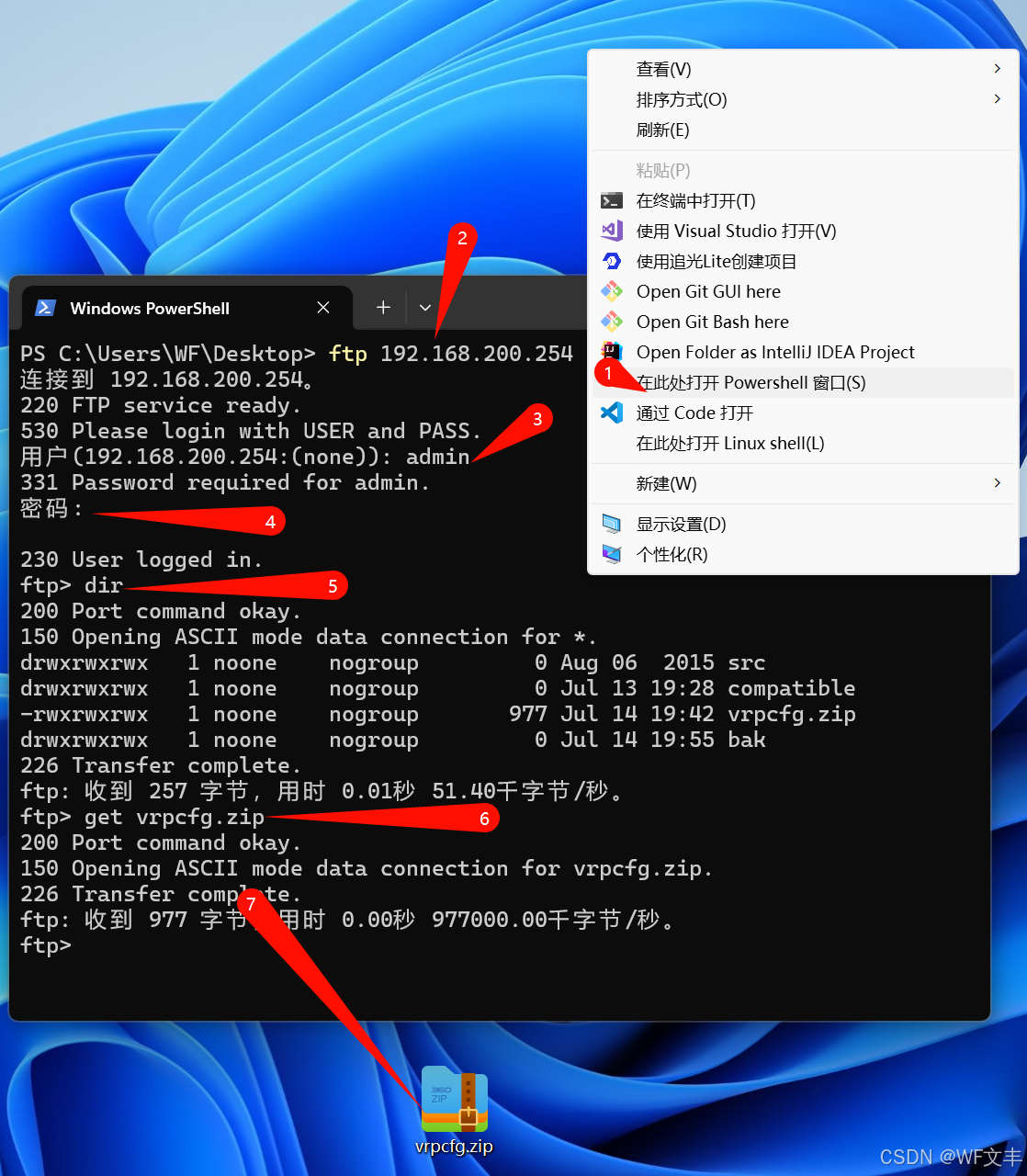
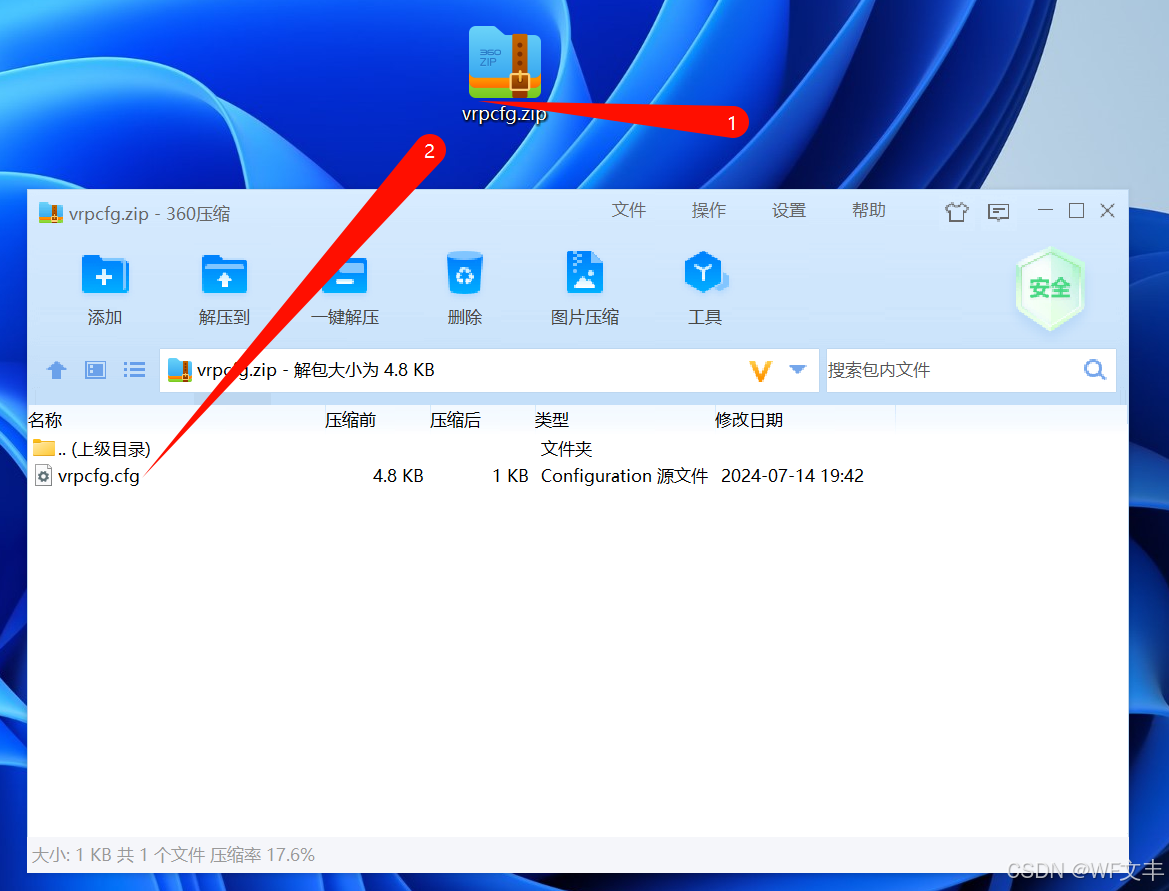
使用FTP备份:
备份配置文件到交换机的flash中。
在交换机上开启FTP服务器,并配置FTP用户。
在PC端通过FTP客户端与设备建立FTP连接,并下载备份的配置文件。
还原配置文件
通过命令行界面:
使用copy命令将备份的配置文件(如TXT文本文件)恢复到交换机中。但直接通过命令行界面恢复TXT文本文件可能不是直接支持的,通常需要将文件上传到交换机的flash中,然后通过命令来加载。
使用图形用户界面(GUI):
登录到交换机的GUI管理界面
导航到配置管理页面或相关的恢复配置选项。
选择要恢复的配置文件,并执行恢复操作。
恢复出厂设置:
登录到交换机的命令行界面。
进入系统配置模式
使用reset factory-configuration命令来恢复出厂设置。这同样会清除所有的业务配置和数据文件。
下面使用ssh及sftp方式演示:
- 登陆ssh
# quit dir 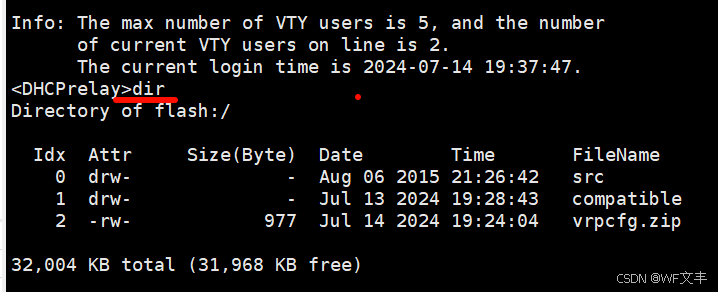
- 保存配置文件
# quit save all 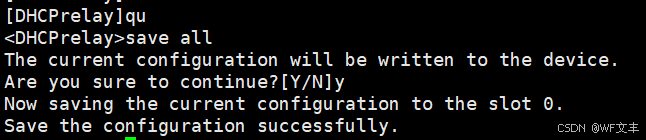
登陆sftp
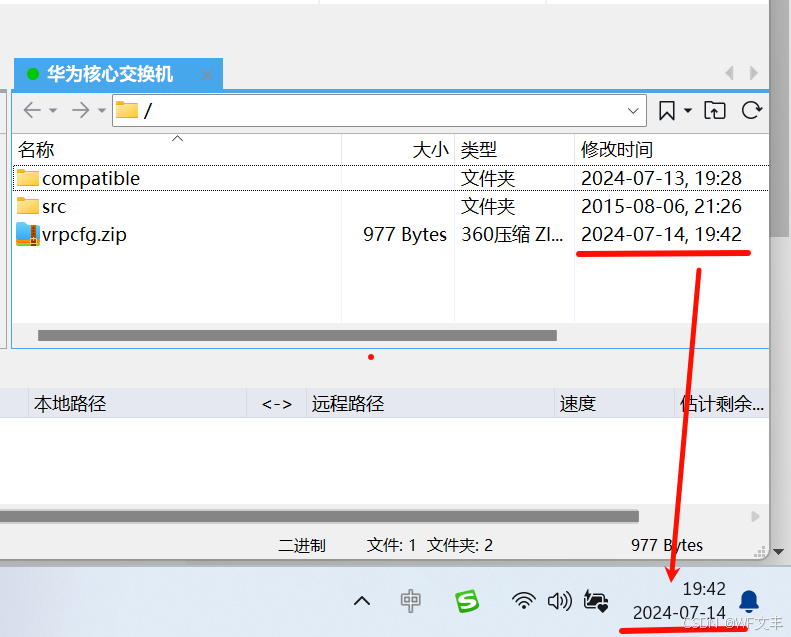
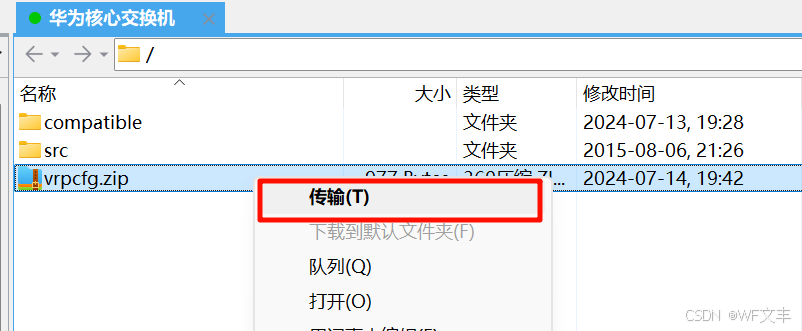
下载
本以为大功告成,结果…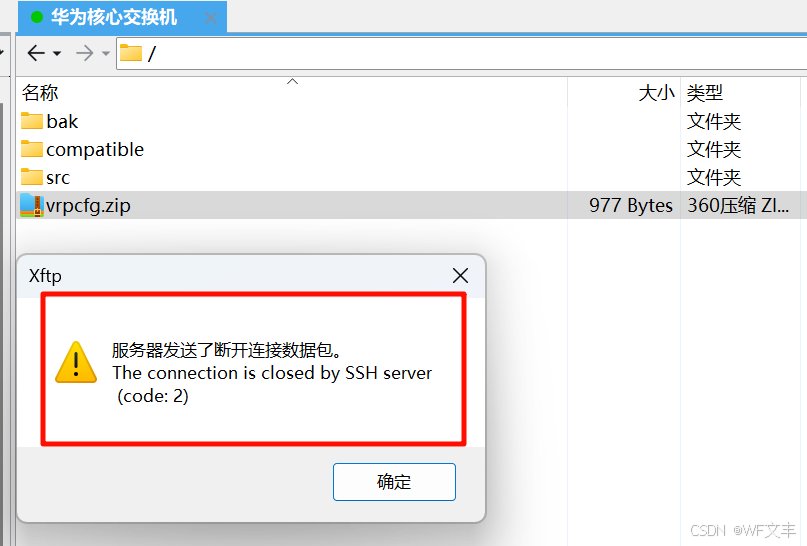
于是尝试ftp(需要在aaa:local-user下配置)
# ftp server enable # aaa local-user admin service-type ftp local-user admin ftp-directory flash:/